OneDrive Connector - Using T-SQL / Linked Server
T-SQL is a programming language used for managing and querying data in Microsoft SQL Server databases. We provides tools for data integration, automation, and connectivity.
If you want to use T-SQL with ZappySys, you can use our Connector, which allows you to connect to SQL Server databases and execute T-SQL queries from OneDrive.
Create Data Source in ZappySys Data Gateway based on API Driver
-
Download and install ODBC PowerPack.
-
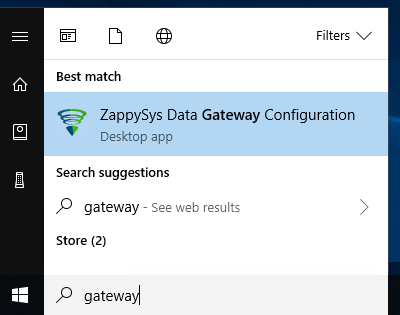
Search for gateway in start menu and Open ZappySys Data Gateway:
-
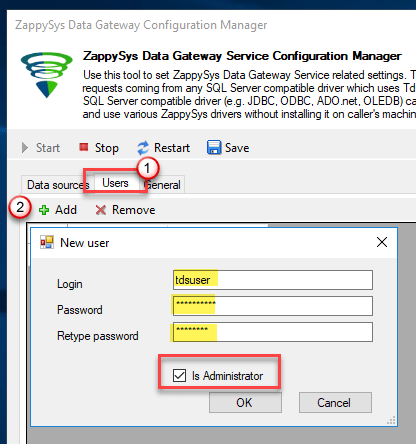
Go to Users Tab to add our first Gateway user. Click Add; we will give it a name tdsuser and enter password you like to give. Check Admin option and click OK to save. We will use these details later when we create linked server:
-
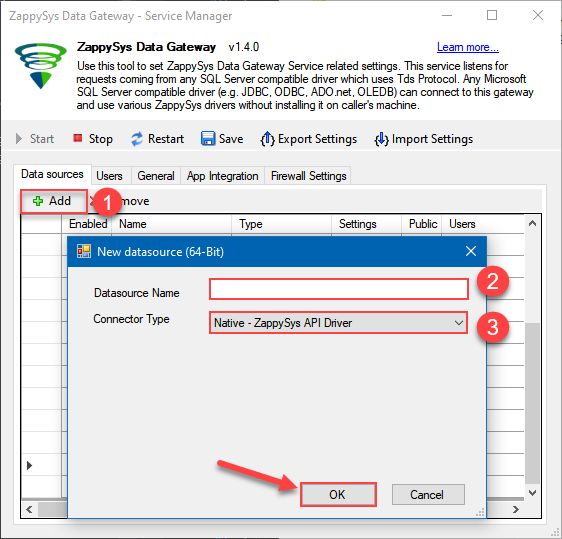
Now we are ready to add a data source. Click Add, give data source a name (Copy this name somewhere, we will need it later) and then select Native - ZappySys API Driver. Finally, click OK. And it will create the Data Set for it and open the ZS driver UI.
OnedriveDSN
-
When the Configuration window appears give your data source a name if you haven't done that already, then select "OneDrive" from the list of Popular Connectors. If "OneDrive" is not present in the list, then click "Search Online" and download it. Then set the path to the location where you downloaded it. Finally, click Continue >> to proceed with configuring the DSN:
OnedriveDSNOneDrive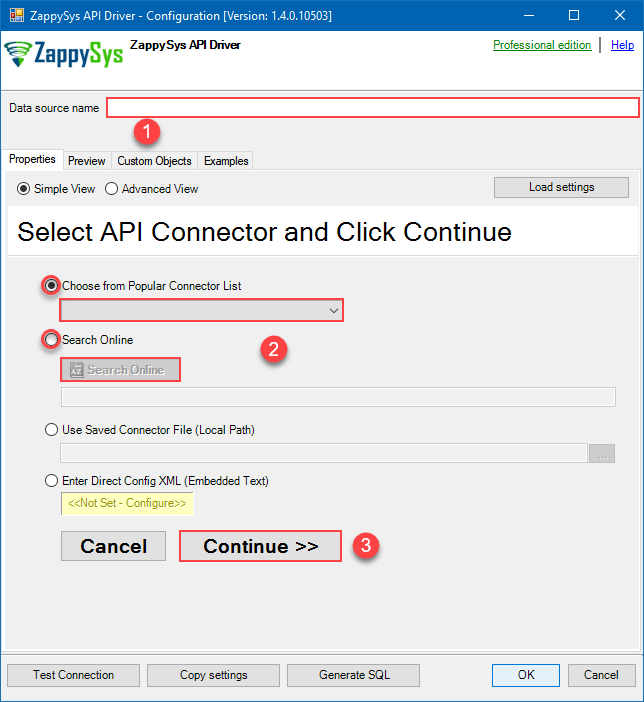
-
Now it's time to configure the Connection Manager. Select Authentication Type, e.g. Token Authentication. Then select API Base URL (in most cases, the default one is the right one). More info is available in the Authentication section.
Use delegated access (User Credentials) whenever you want to let a signed-in user work with their own resources or resources they can access. Whether it's an admin setting up policies for their entire organization or a user deleting an email in their inbox, all scenarios involving user actions should use delegated access. [API reference]
Steps how to get and use OneDrive credentials
Follow these simple steps below to create Microsoft Entra ID application with delegated access:
WARNING: To automate your company's processes, make sure you use a system/generic account (e.g.automation@my-company.com). When you use a personal account which is tied to a specific employee profile and that employee leaves the company, the token may become invalid and any automated processes using that token will start to fail.- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
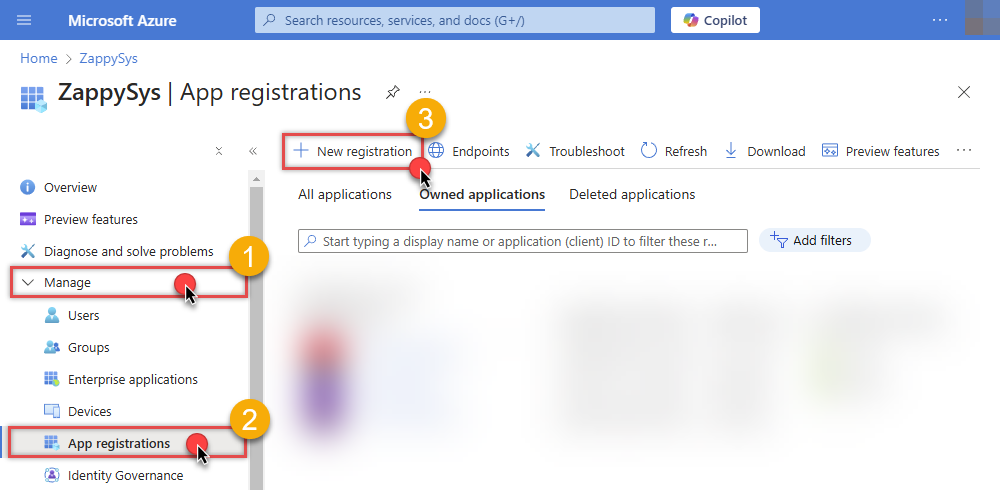
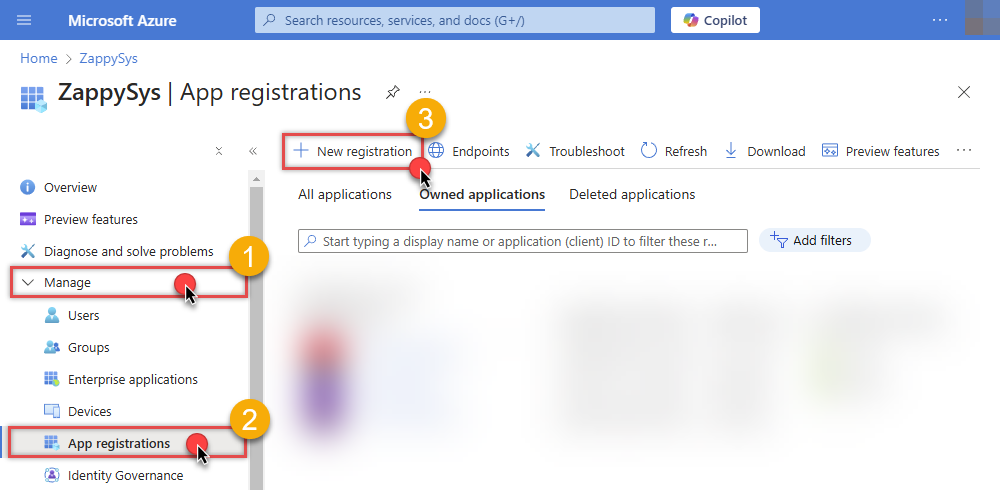
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
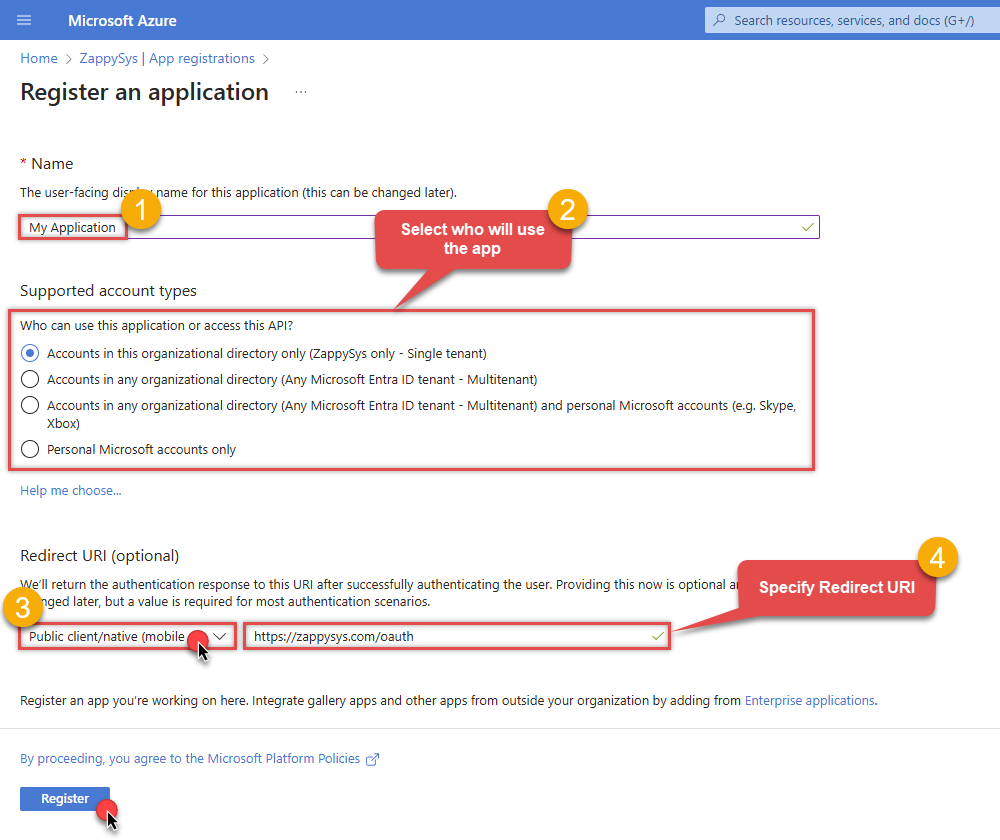
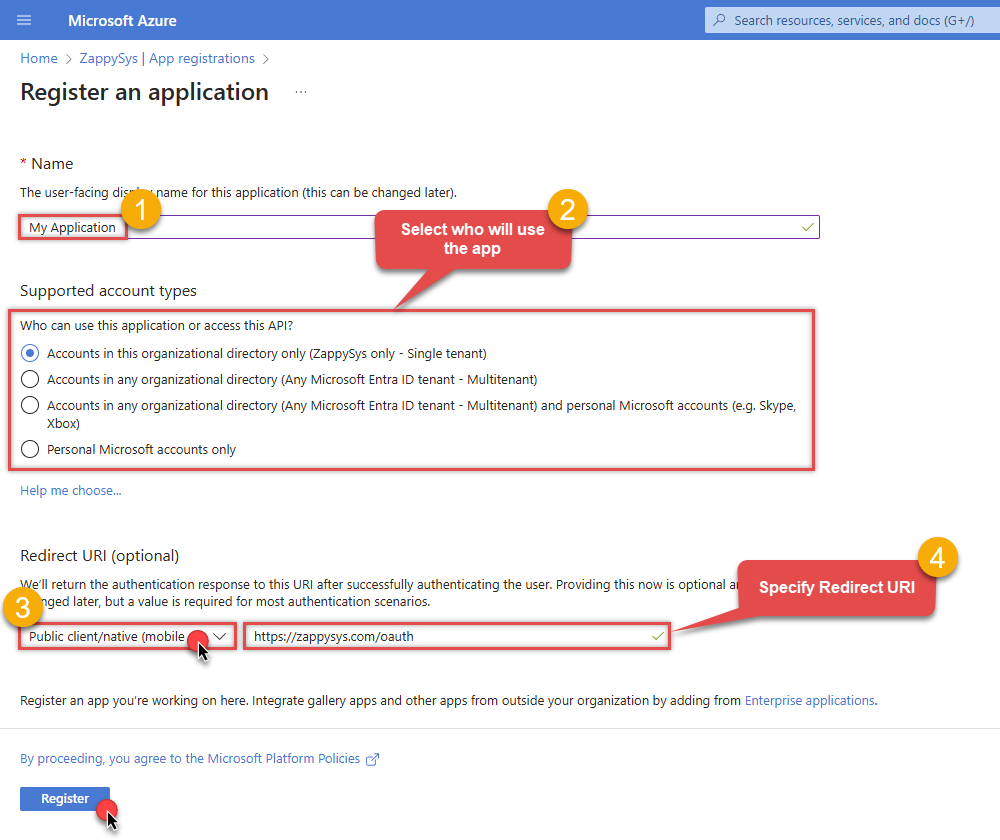
When configuration window opens, configure these fields:
-
Supported account type
- Use
Accounts in this organizational directory only, if you need access to data in your organization only.
- Use
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Use
https://zappysys.com/oauthas the URL.
- Set the type to
-
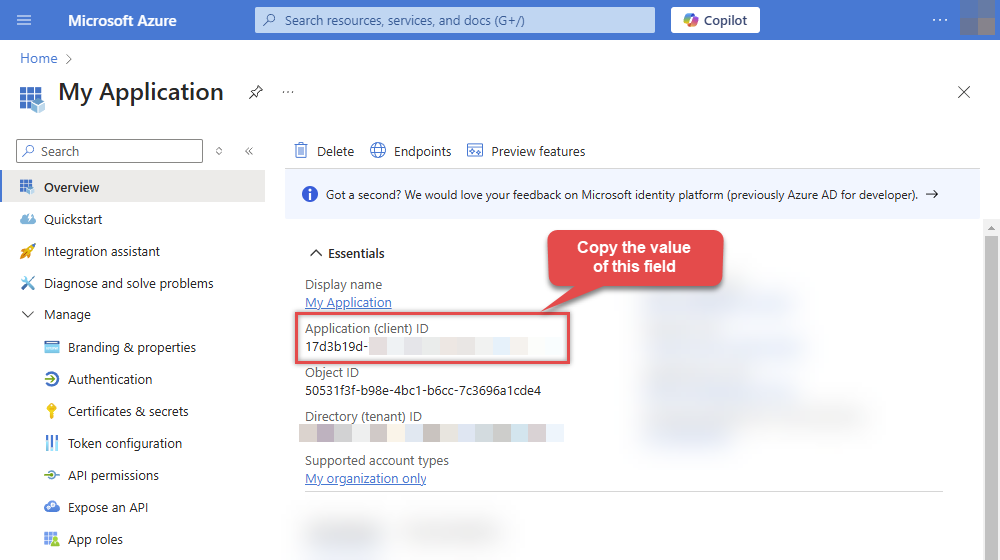
After registering the app, copy the Application (client) ID for later:
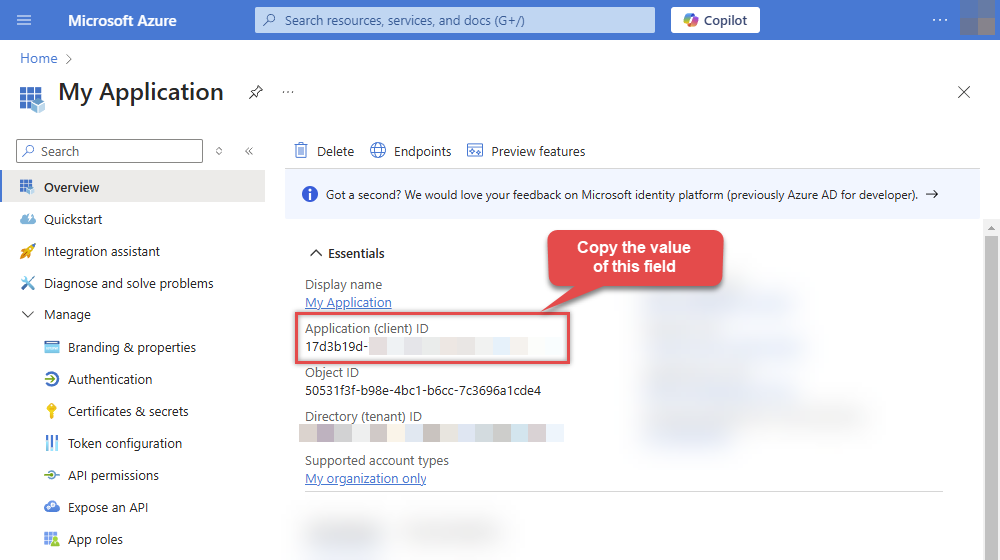
-
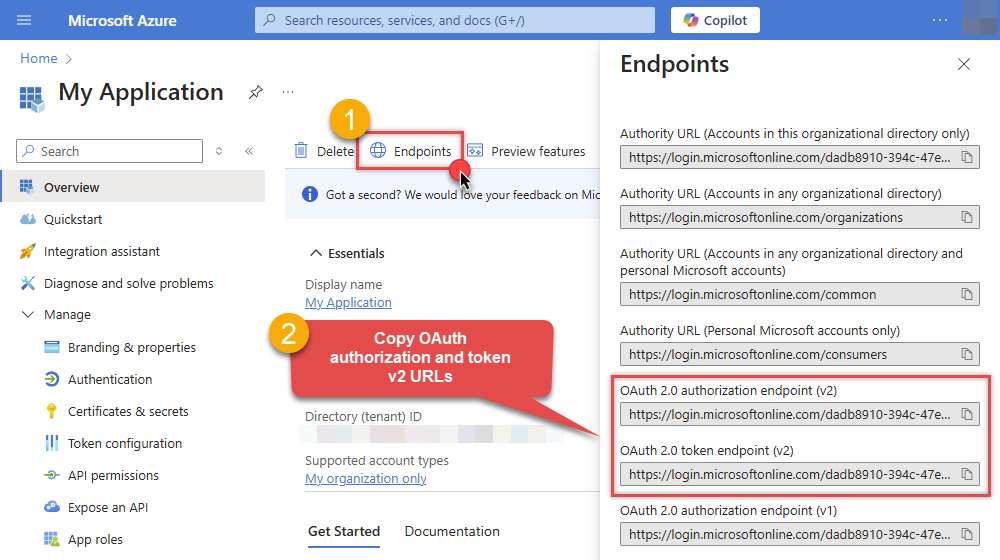
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs to use later in the configuration:
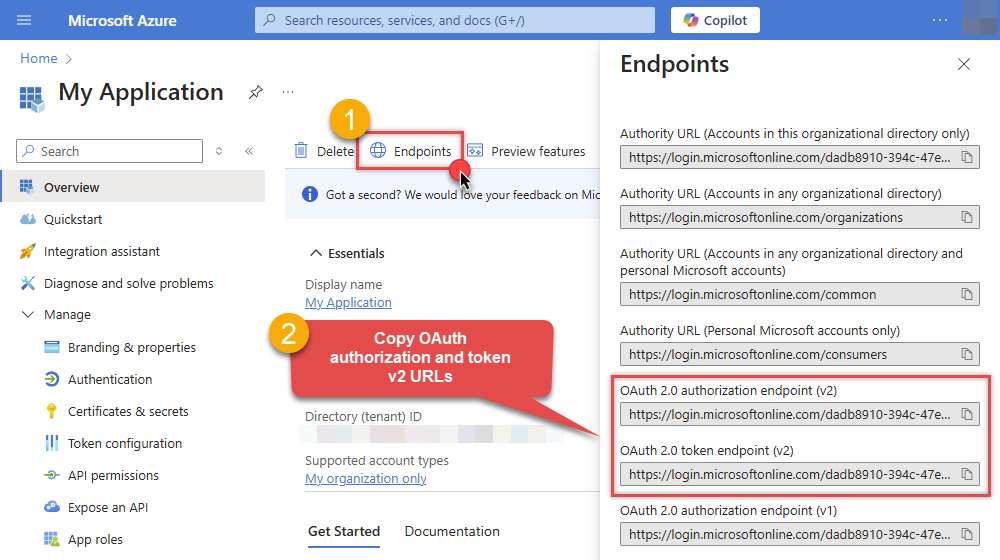
-
Now go to SSIS package or ODBC data source and use the copied values in User Credentials authentication configuration:
- In the Authorization URL field paste the OAuth authorization endpoint (v2) URL value you copied in the previous step.
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
-
In the Scope field use the default value or select individual scopes, e.g.:
-
email -
offline_access -
openid -
profile -
User.Read -
Files.Read.All -
Files.ReadWrite.All
-
- Press Generate Token button to generate Access and Refresh Tokens.
- Optional step. Choose Default Site Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Now you are ready to use the API Connector!
Fill in all required parameters and set optional parameters if needed:
OnedriveDSNOneDriveUser Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Authorization URL Fill-in the parameter... Token URL Fill-in the parameter... Client ID Fill-in the parameter... Scope Fill-in the parameter... Optional Parameters Client Secret Refresh Token File Path Return URL https://zappysys.com/oauth Default Group or User Id (additional Scopes needed to list - If fails enter manually) Default Drive Id (Select after clicking **Generate Token**) me RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Login Prompt Option Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 0 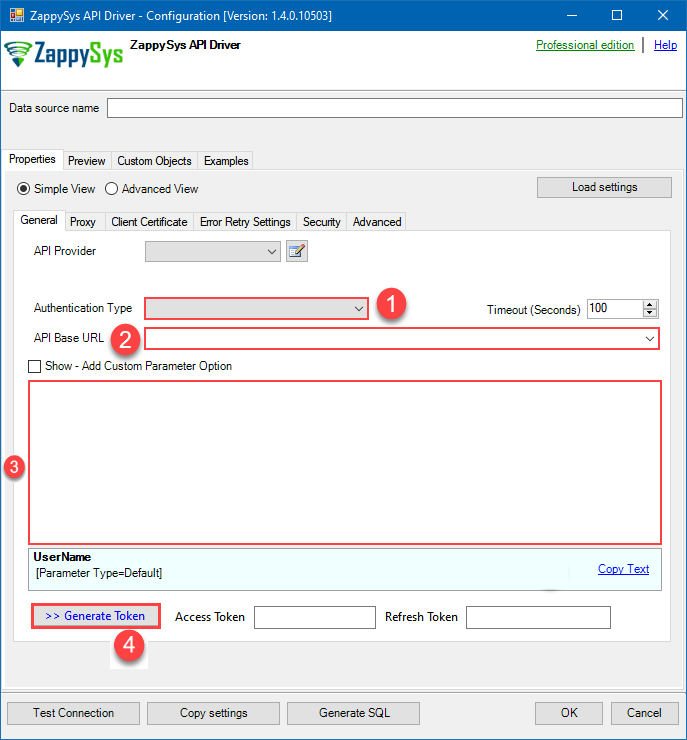
Application-only access is broader and more powerful than delegated access (User Credentials), so you should only use app-only access where needed. Use it when: 1. The application needs to run in an automated way, without user input (for example, a daily script that checks emails from certain contacts and sends automated responses). 2. The application needs to access resources belonging to multiple different users (for example, a backup or data loss prevention app might need to retrieve messages from many different chat channels, each with different participants). 3. You find yourself tempted to store credentials locally and allow the app to sign in 'as' the user or admin. [API reference]
Steps how to get and use OneDrive credentials
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access Full site(s), List(s), List Item(s) and File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Leave the URL field empty.
- Set the type to
-
After registering the app, copy the Application (client) ID for later:
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
-
Continue and create Client secret:
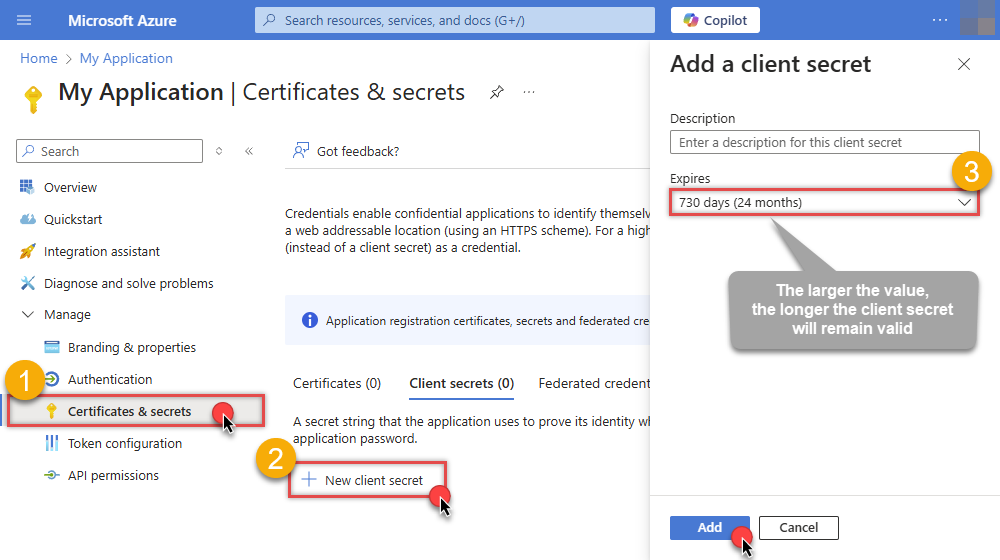
-
Then copy the Client secret for later steps:
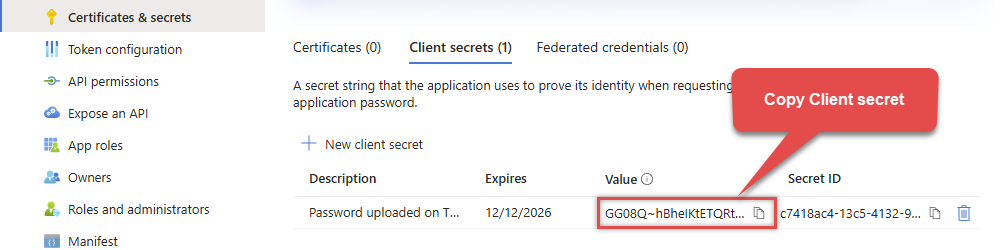
-
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
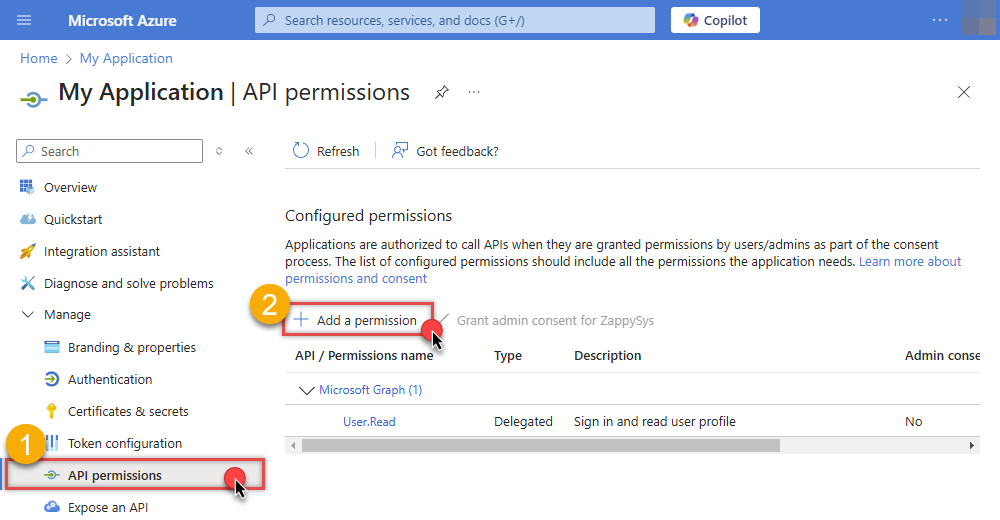
-
Select Microsoft Graph:
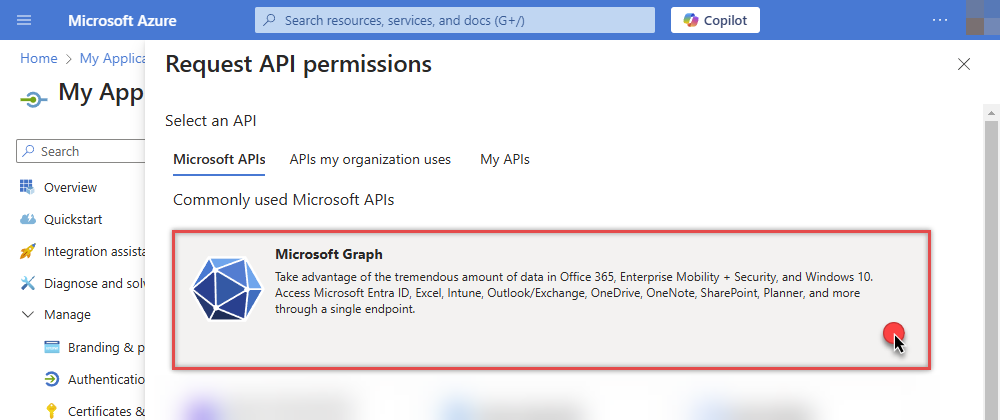
-
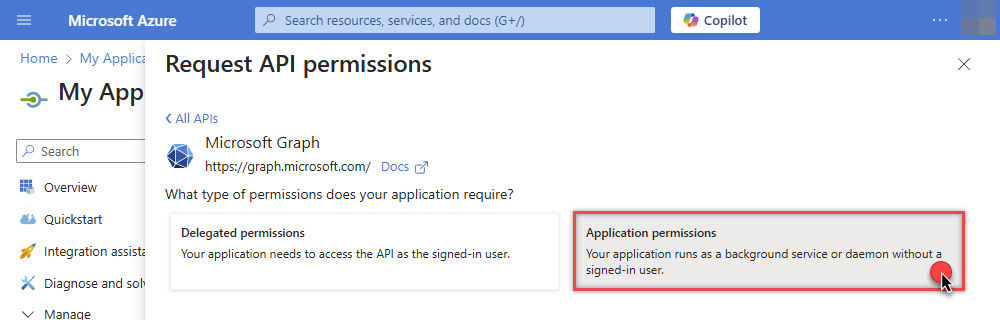
Then choose Application permissions option:
-
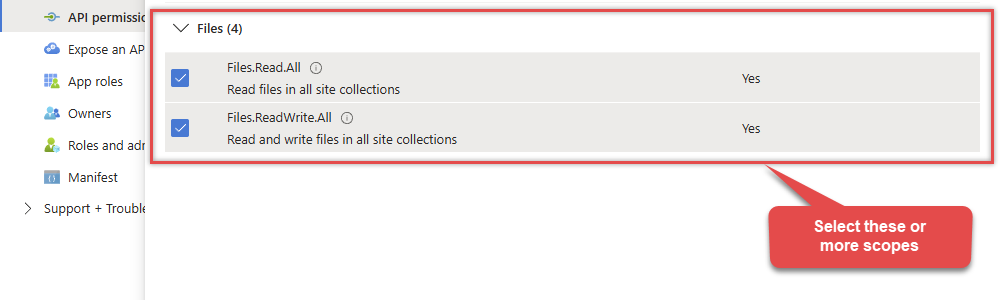
Continue by adding these Files (OneDrive) permissions (Just search for "Site" and then select desired permissions):
-
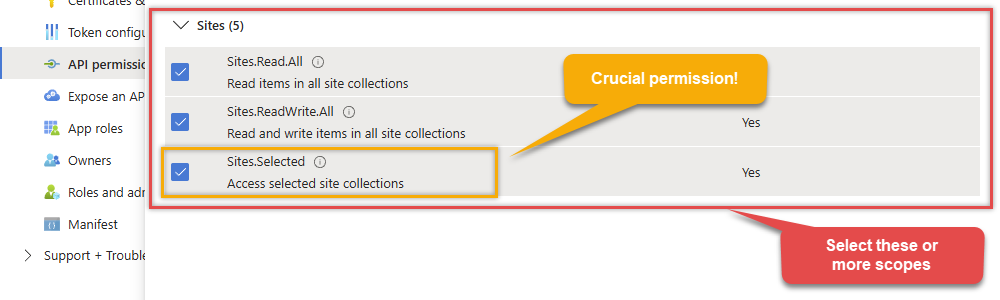
Move on by addding these Sites (SharePoint) permissions (You can search for "Site" and then select desired permissions):
-
Finish by clicking Add permissions button:

-
Now it's time to Grant admin consent for your application:
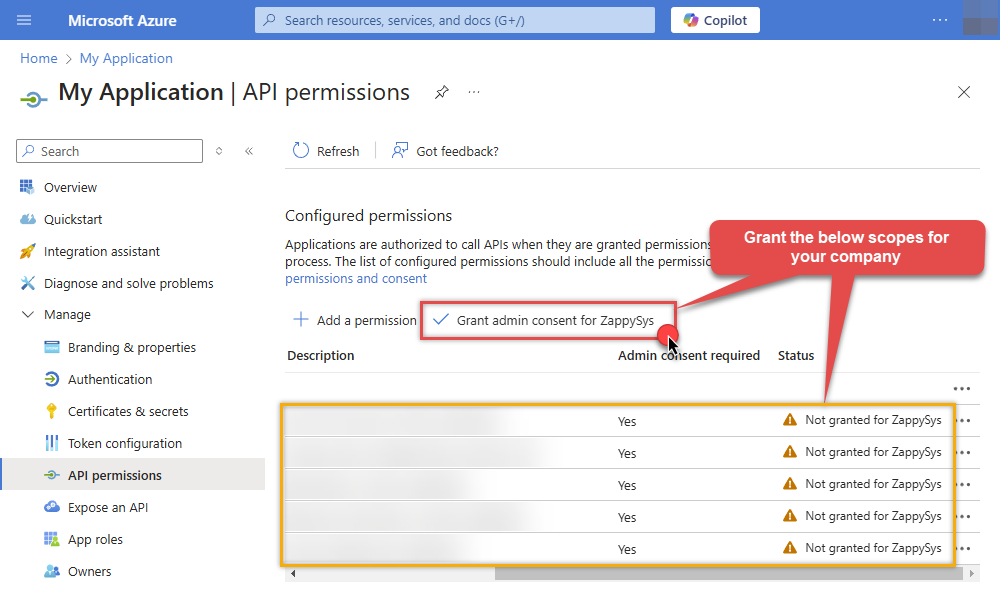
-
Confirm all the permissions are granted:
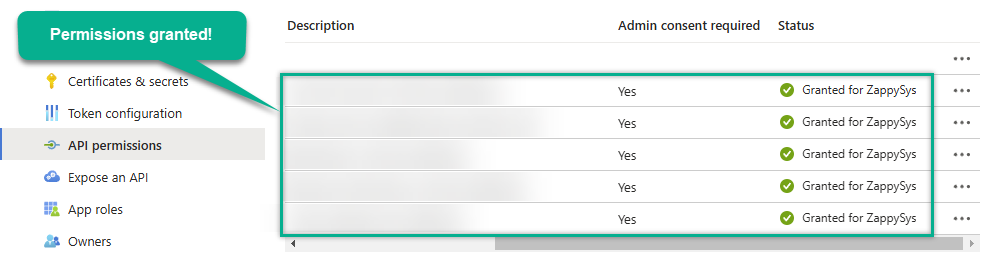
-
Now go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- In the Client Secret field paste the Client secret value you copied in the previous step.
- Optional step. Choose Default Site Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Let's move on to the next step.
Step-2 (Method#1 - New Approach): Grant permission to app using permission API (UI is not available yet)
In year 2024 microsoft launched
*.Selected
permission scopes and new APIs to grant granular permissions to the resource for app access scenario. Unfortunatly, there is no User interface available yet to control this access so you have to call Admin API or use PowerShell script to control this. [Click here to learn more]. Follow these simple steps to configure permissions for app we created earlier (steps assume you are the owner of the resource and like to grant some permissions e.g. read, write, full, owner):- Open PowerShell (Run as Admin user)
- Install Graph API module by running this command
Import-Module Microsoft.Graph.Sites - Now you can call following PowerShell code to set "read" and "write" permission for the app we created earlier (assuming app id is 89ea5c94-7736-4e25-95ad-3fa95f62b66e).
#More info https://learn.microsoft.com/en-us/graph/permissions-selected-overview?tabs=powershell #Step-1: Install module if not found #Install-Module Microsoft.Graph.Sites #Step-2: set permission for app 89xxx6e and site zappysys.xx.efcdd21xxxxe2 Import-Module Microsoft.Graph.Sites #Step-3: Login Connect-MgGraph #Step-4: Set Parameters for API Call (set Permissions, SiteId and AppId - Replace under #TODO) You can find SiteId by visiting this URL in browser (assuming you visted SharePoint site and already logged in) https://{your-company}.sharepoint.com/_api/site --OR-- for sub-site use https://{your-company}.sharepoint.com/sites/{your-site}/_api/site. Find Id from the response (e.g. <Id m:type="Edm.Guid">) $siteId="yourcompany.sharepoint.com,efcddxxxxxxx104d8b5e3,8c9c6xxxxxxxx84e2" #--OR-- simple id #$siteId="efcddxxxxxxx104d8b5e3" $params = @{ roles = @( #possible options are read, write, fullcontrol, owner (write includes read too) #TODO: Change here "write" ) grantedTo = @{ application = @{ #find this Client Id (Application Id) from the Azure Portal - Application page (https://portal.azure.com/#view/Microsoft_AAD_RegisteredApps/ApplicationsListBlade) #TODO: Change here id = "c3e9xxxxxx-xxxxx-xxxxx-xxxx-xxxxxb30c1" } } } #Step-5: Grant Permission New-MgSitePermission -SiteId $siteId -BodyParameter $params
Fill in all required parameters and set optional parameters if needed:
OnedriveDSNOneDriveApplication Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Client Secret Fill-in the parameter... Default Group or User Id (additional Scopes needed to list - If fails enter manually) Fill-in the parameter... Default Drive Id Fill-in the parameter... Optional Parameters Scope https://graph.microsoft.com/.default RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1 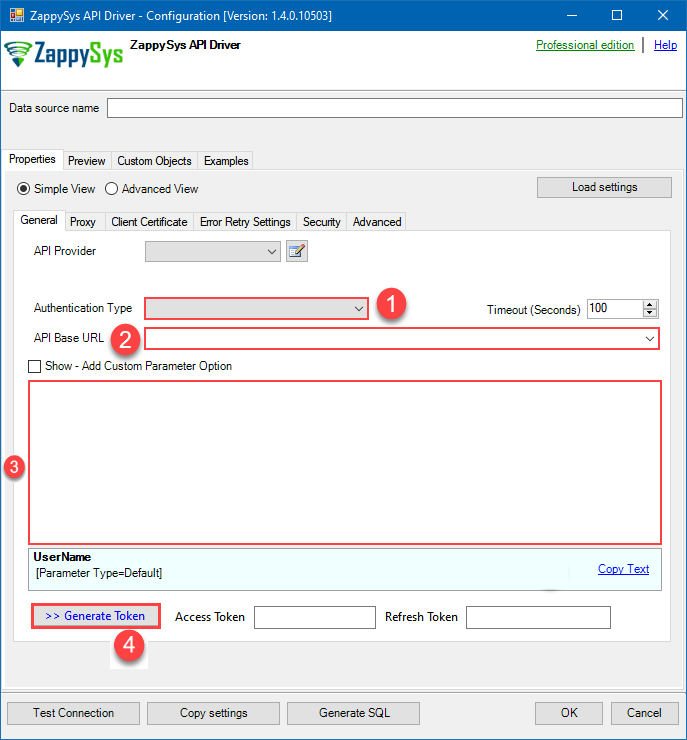 Steps how to get and use OneDrive credentials
Steps how to get and use OneDrive credentials
To use Certificate-Based Authentication Setup please follow the steps listed in [Application Credentials] authentication and once done come back here to finish next stsps.This guide walks you through setting up a certificate-based authentication flow for Microsoft Graph or other Azure AD protected APIs using client credentials and a JWT.
Step 1: Generate a Self-Signed Certificate
You can use OpenSSL or any other way to generate Certificate file but make it simple below example uses PowerShell. Open PowerShell and execute code listed in below steps.# Run this in PowerShell #Change .AddYears(1) to desired number. By default it expires certificate in one year as per below code. $cert = New-SelfSignedCertificate ` -Subject "CN=MyClientAppCert" ` -KeySpec Signature ` -KeyExportPolicy Exportable ` -KeyLength 2048 ` -CertStoreLocation "Cert:\CurrentUser\My" ` -KeyAlgorithm RSA ` -HashAlgorithm SHA256 ` -NotAfter (Get-Date).AddYears(1) ` -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider" # Export private key (.pfx) - Keep this with you to make API calls (SECRET KEY - DONOT SHARE) $pfxPath = "$env:USERPROFILE\Desktop\private_key.pfx" $pwd = ConvertTo-SecureString -String "yourStrongPassword123" -Force -AsPlainText Export-PfxCertificate -Cert $cert -FilePath $pfxPath -Password $pwd # Export public certificate (.cer) - UPLOAD this to Azure Portal $cerPath = "$env:USERPROFILE\Desktop\public_key.cer" Export-Certificate -Cert $cert -FilePath $cerPathStep 2: Register or Configure an App in Azure AD
- Go to https://portal.azure.com
- Navigate to Azure Active Directory > App registrations
- Click + New registration or open an existing app
- Copy the Application (client) ID and Directory (tenant) ID
Step 3: Upload the Certificate
- In your App Registration, go to Certificates & secrets
- Under Certificates, click Upload certificate
- Select the
.cerfile (public certificate) - Click Add
Step 4: Grant API Permissions
- Go to the API permissions tab
- Click Add a permission
- Select Microsoft Graph (or another API)
- Choose Application permissions
- Add scopes such as:
-
Sites.Read.All -
Sites.ReadWrite.All -
Files.Read.All -
Files.ReadWrite.All -
email -
offline_access -
openid -
profile -
User.Read
-
- Click Grant admin consent (requires admin)
Step 5: Use PFX file
Once both files generated perform the following steps to use PFX file., , Use the Certificate file (*.pfx) Now its time to use pfx file generated in the previous step. PFX file contains private key and public key both.- On ZappySys Connection UI Go to
Certificate Tab - Change Storage Mode to Local PFX File (or you can Import PFX file in Certificate Storage - User Store / Machine Store and use that way)
- Supply the pfx file path or select certificate from Local Certificate Store if you imported that way in earlier step
- Supply the certificate password (same password used in earlier PowerShell script)
- Test connection see everything is good
Fill in all required parameters and set optional parameters if needed:
OnedriveDSNOneDriveApplication Credentials with Certificate (Sign JWT with Private Key) [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Certificate: *** Configure [Client Certificate] Tab *** Fill-in the parameter... Default Site Id Fill-in the parameter... Optional Parameters Default Drive Id RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1 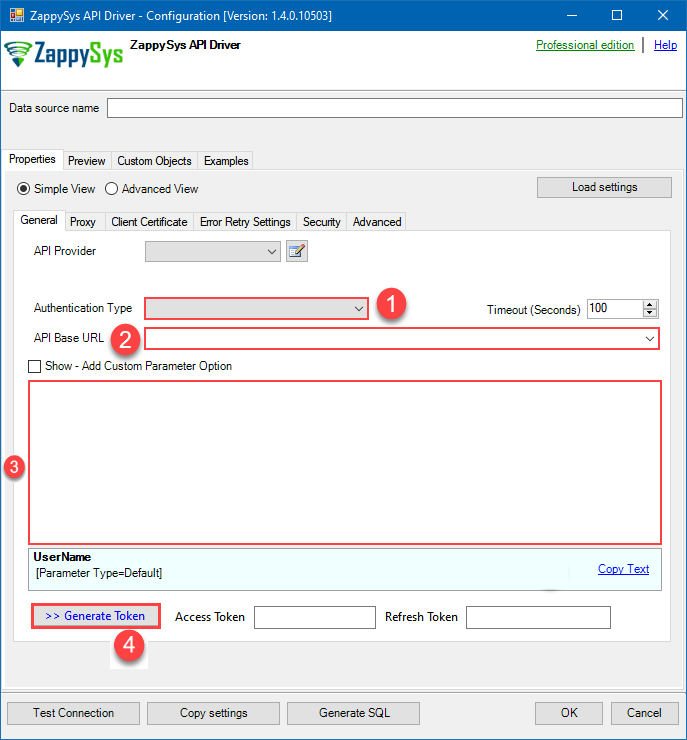
-
Once the data source connection has been configured, it's time to configure the SQL query. Select the Preview tab and then click Query Builder button to configure the SQL query:
 - OneDriveOneDrive Connector can be used to integrate OneDrive and your defined data source, e.g. Microsoft SQL, Oracle, Excel, Power BI, etc. Get, write, delete OneDrive data in a few clicks!OnedriveDSN
- OneDriveOneDrive Connector can be used to integrate OneDrive and your defined data source, e.g. Microsoft SQL, Oracle, Excel, Power BI, etc. Get, write, delete OneDrive data in a few clicks!OnedriveDSN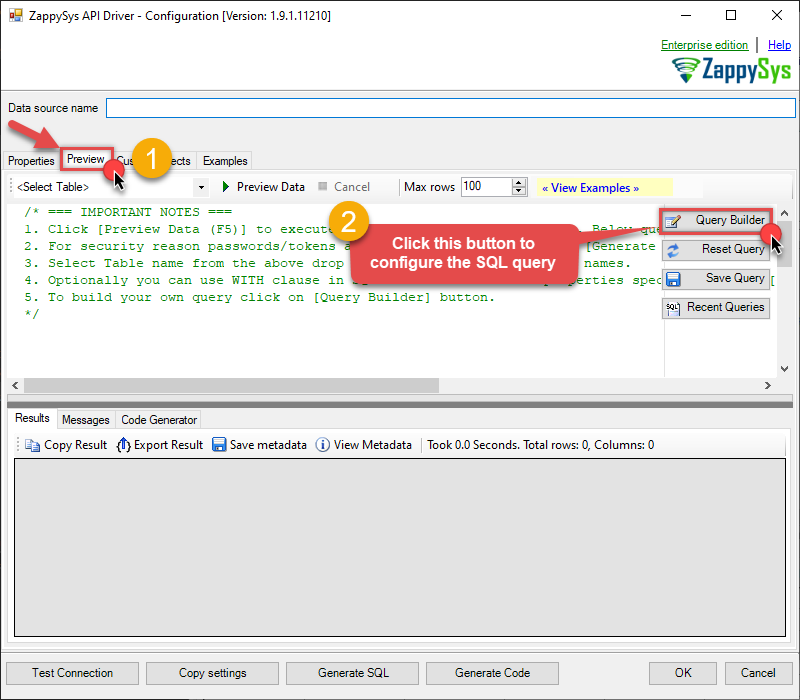
-
Start by selecting the Table or Endpoint you are interested in and then configure the parameters. This will generate a query that we will use in to retrieve data from OneDrive. Hit OK button to use this query in the next step.
SELECT * FROM Files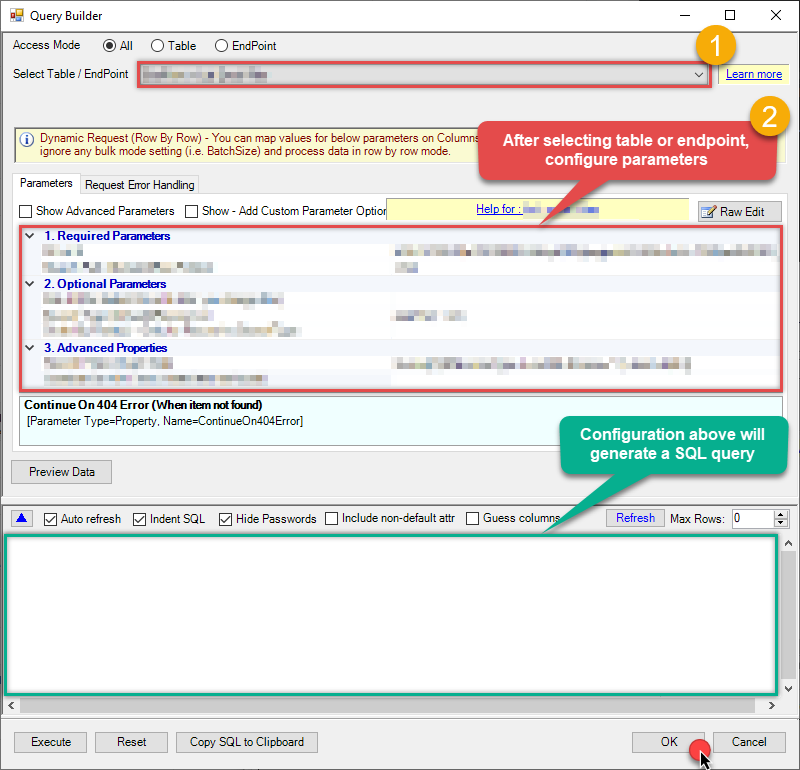 Some parameters configured in this window will be passed to the OneDrive API, e.g. filtering parameters. It means that filtering will be done on the server side (instead of the client side), enabling you to get only the meaningful data
Some parameters configured in this window will be passed to the OneDrive API, e.g. filtering parameters. It means that filtering will be done on the server side (instead of the client side), enabling you to get only the meaningful datamuch faster . -
Now hit Preview Data button to preview the data using the generated SQL query. If you are satisfied with the result, use this query in :
 - OneDriveOneDrive Connector can be used to integrate OneDrive and your defined data source, e.g. Microsoft SQL, Oracle, Excel, Power BI, etc. Get, write, delete OneDrive data in a few clicks!OnedriveDSN
- OneDriveOneDrive Connector can be used to integrate OneDrive and your defined data source, e.g. Microsoft SQL, Oracle, Excel, Power BI, etc. Get, write, delete OneDrive data in a few clicks!OnedriveDSNSELECT * FROM Files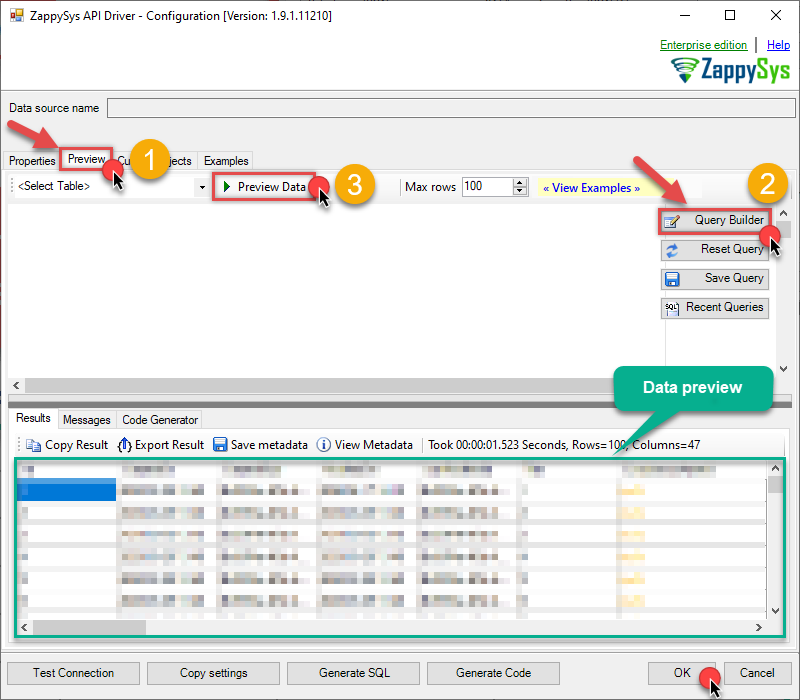 You can also access data quickly from the tables dropdown by selecting <Select table>.A
You can also access data quickly from the tables dropdown by selecting <Select table>.AWHEREclause,LIMITkeyword will be performed on the client side, meaning that thewhole result set will be retrieved from the OneDrive API first, and only then the filtering will be applied to the data. If possible, it is recommended to use parameters in Query Builder to filter the data on the server side (in OneDrive servers). -
Click OK to finish creating the data source.
Read data in SQL Server using ZappySys Data Gateway
To read the data in SQL Server, the first thing you have to do is create a Linked Server:
-
First, let's open SQL Server Management Studio, create a new Linked Server, and start configuring it:
LS_TO_ONEDRIVE_IN_GATEWAYMicrosoft OLE DB Driver for SQL Serverlocalhost,5000OnedriveDSNOnedriveDSN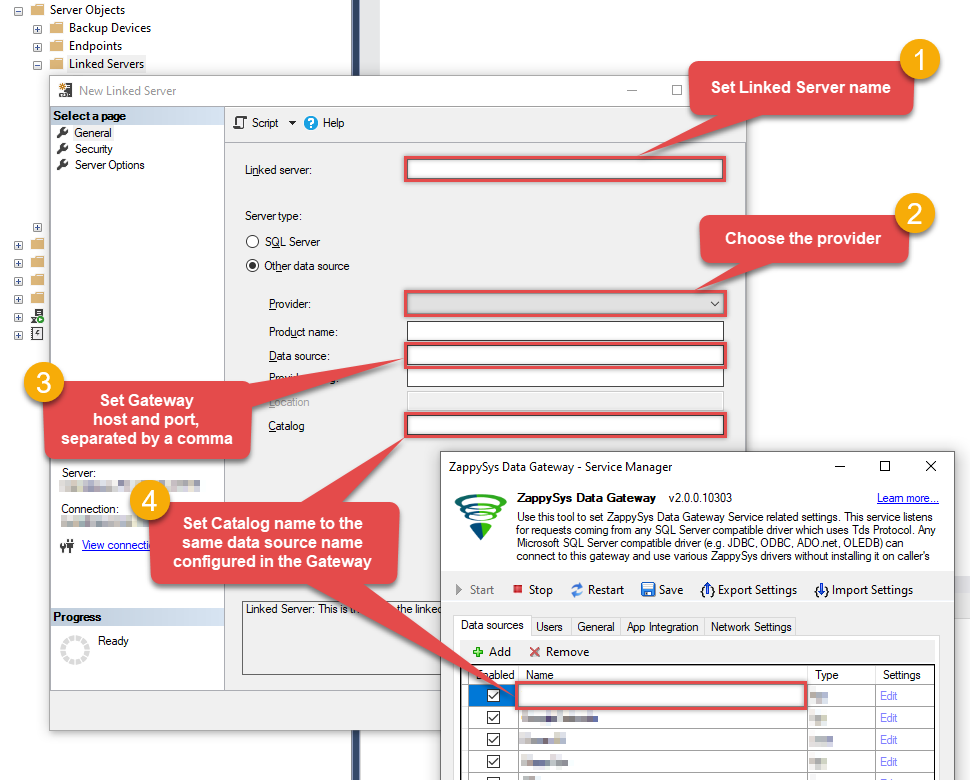 Choose SQL Server Native Client 11.0 as Provider if you don't see the option shown above.
Choose SQL Server Native Client 11.0 as Provider if you don't see the option shown above. -
Then click on Security option and configure username we created in ZappySys Data Gateway in one of the previous steps:
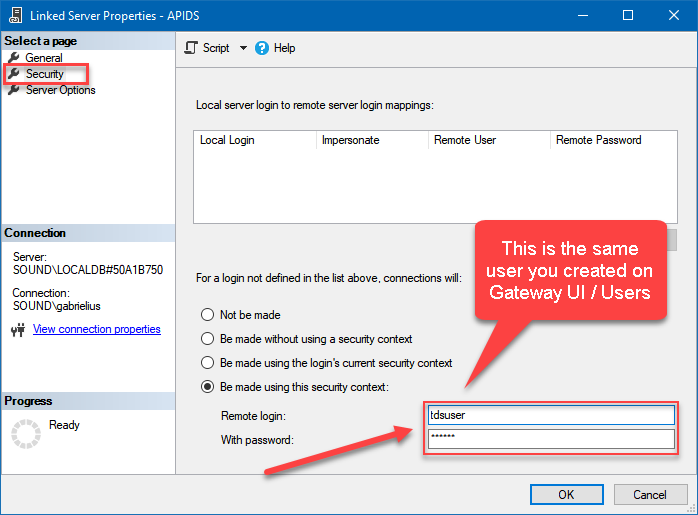
-
Optional step. Under the Server Options, Enable RPC and RPC Out and Disable Promotion of Distributed Transactions(MSDTC).
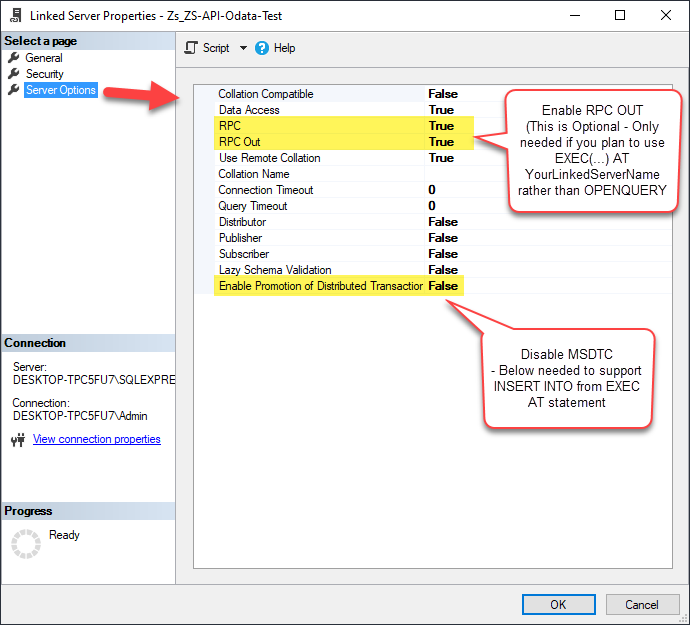
You need to enable RPC Out if you plan to use
EXEC(...) AT [LS_TO_ONEDRIVE_IN_GATEWAY]rather than OPENQUERY.
If don't enabled it, you will encounter theServer 'LS_TO_ONEDRIVE_IN_GATEWAY' is not configured for RPCerror.Query Example:
EXEC('SELECT * FROM Files') AT [LS_TO_ONEDRIVE_IN_GATEWAY]
If you plan to use
'INSERT INTO <TABLE> EXEC(...) AT [LS_TO_ONEDRIVE_IN_GATEWAY]'in that case you need to Disable Promotion of Distributed Transactions(MSDTC).
If don't disabled it, you will encounter theThe operation could not be performed because OLE DB provider "SQLNCLI11" for linked server "MY_LINKED_SERVER_NAME" was unable to begin a distributed transaction.error.Query Example:
INSERT INTO dbo.Products EXEC('SELECT * FROM Files') AT [LS_TO_ONEDRIVE_IN_GATEWAY] -
Finally, open a new query and execute a query we saved in one of the previous steps:
SELECT * FROM OPENQUERY([LS_TO_ONEDRIVE_IN_GATEWAY], 'SELECT * FROM Files')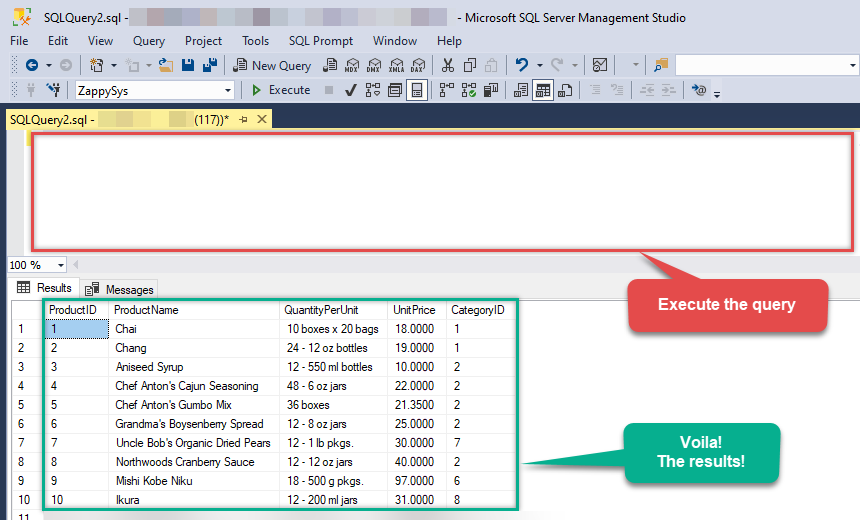
SELECT * FROM OPENQUERY([LS_TO_ONEDRIVE_IN_GATEWAY], 'SELECT * FROM Files')
Create Linked Server using Code
In previous section you saw how to create a Linked Server from UI. You can do similar action by code too (see below). Run below script after changing necessary parameters. Assuming your Data Source name on ZappySys Data Gateway UI is 'OnedriveDSN'USE [master]
GO
--///////////////////////////////////////////////////////////////////////////////////////
--Run below code in SSMS to create Linked Server and use ZappySys Drivers in SQL Server
--///////////////////////////////////////////////////////////////////////////////////////
-- Replace YOUR_GATEWAY_USER, YOUR_GATEWAY_PASSWORD
-- Replace localhost with IP/Machine name if ZappySys Gateway Running on different machine other than SQL Server
-- Replace Port 5000 if you configured gateway on a different port
--1. Configure your gateway service as per this article https://zappysys.com/links?id=10036
--2. Make sure you have SQL Server Installed. You can download FREE SQL Server Express Edition from here if you dont want to buy Paid version https://www.microsoft.com/en-us/sql-server/sql-server-editions-express
--Uncomment below if you like to drop linked server if it already exists
--EXEC master.dbo.sp_dropserver @server=N'LS_TO_ONEDRIVE_IN_GATEWAY', @droplogins='droplogins'
--3. Create new linked server
EXEC master.dbo.sp_addlinkedserver
@server = N'LS_TO_ONEDRIVE_IN_GATEWAY' --Linked server name (this will be used in OPENQUERY sql
, @srvproduct=N''
---- For MSSQL 2012,2014,2016 and 2019 use below (SQL Server Native Client 11.0)---
, @provider=N'SQLNCLI11'
---- For MSSQL 2022 or higher use below (Microsoft OLE DB Driver for SQL Server)---
--, @provider=N'MSOLEDBSQL'
, @datasrc=N'localhost,5000' --//Machine / Port where Gateway service is running
, @provstr=N'Network Library=DBMSSOCN;'
, @catalog=N'OnedriveDSN' --Data source name you gave on Gateway service settings
--4. Attach gateway login with linked server
EXEC master.dbo.sp_addlinkedsrvlogin
@rmtsrvname=N'LS_TO_ONEDRIVE_IN_GATEWAY' --linked server name
, @useself=N'False'
, @locallogin=NULL
, @rmtuser=N'YOUR_GATEWAY_USER' --enter your Gateway user name
, @rmtpassword='YOUR_GATEWAY_PASSWORD' --enter your Gateway user's password
GO
--5. Enable RPC OUT (This is Optional - Only needed if you plan to use EXEC(...) AT YourLinkedServerName rather than OPENQUERY
EXEC sp_serveroption 'LS_TO_ONEDRIVE_IN_GATEWAY', 'rpc', true;
EXEC sp_serveroption 'LS_TO_ONEDRIVE_IN_GATEWAY', 'rpc out', true;
--Disable MSDTC - Below needed to support INSERT INTO from EXEC AT statement
EXEC sp_serveroption 'LS_TO_ONEDRIVE_IN_GATEWAY', 'remote proc transaction promotion', false;
--Increase query timeout if query is going to take longer than 10 mins (Default timeout is 600 seconds)
--EXEC sp_serveroption 'LS_TO_ONEDRIVE_IN_GATEWAY', 'query timeout', 1200;
GO