How to integrate OneDrive using SSIS


Learn how to quickly and efficiently connect OneDrive with SSIS for smooth data access.
Read and write Microsoft OneDrive data effortlessly. Integrate, manage, and automate files and folders — almost no coding required. You can do it all using the high-performance OneDrive Connector. We'll walk you through the entire setup.
Ready to dive in? Download the product to jump right in, or follow the step-by-step guide below to see how it works.
Video tutorial
Watch this quick video to see the integration in action. It walks you through the end-to-end setup, including:
- Installing the SSIS PowerPack
- Configuring a secure connection to OneDrive
- Working with OneDrive data directly inside SSIS
- Exploring advanced API Source features
Once you are done watching, simply follow the step-by-step written guide below to configure your data source.
Prerequisites
Before we begin, make sure the following prerequisites are met:
- SSIS designer installed. Sometimes it is referred as BIDS or SSDT (download it from Microsoft).
- Basic knowledge of SSIS package development using Microsoft SQL Server Integration Services.
- SSIS PowerPack is installed (if you are new to SSIS PowerPack, then get started!).
Read data from OneDrive in SSIS (Export data)
In this section we will learn how to configure and use OneDrive Connector in API Source to extract data from OneDrive.
-
Open Visual Studio and click Create a new project.
-
Select Integration Services Project. Enter a name and location for your project, then click OK.
-
From the SSIS Toolbox, drag and drop a Data Flow Task onto the Control Flow surface, and double-click it:

-
Make sure you are in the Data Flow Task designer:

-
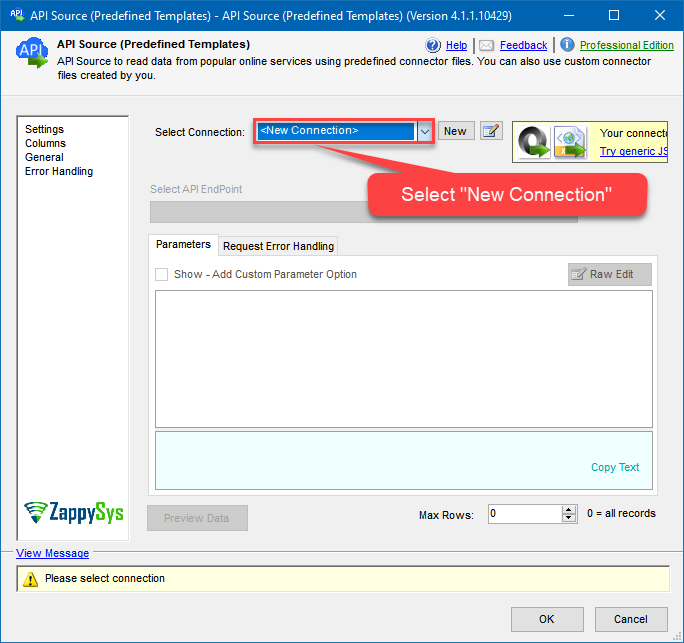
From the SSIS toolbox drag and API Source (Predefined Templates) on the data flow designer surface, and double click on it to edit it:

-
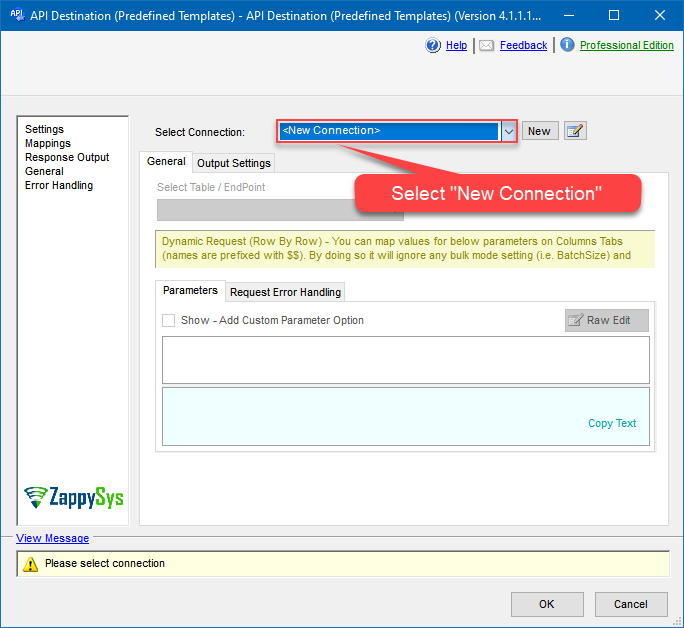
Select New Connection to create a new connection:
-
Use a preinstalled OneDrive Connector from Popular Connector List or press Search Online radio button to download OneDrive Connector. Once downloaded simply use it in the configuration:
OneDrive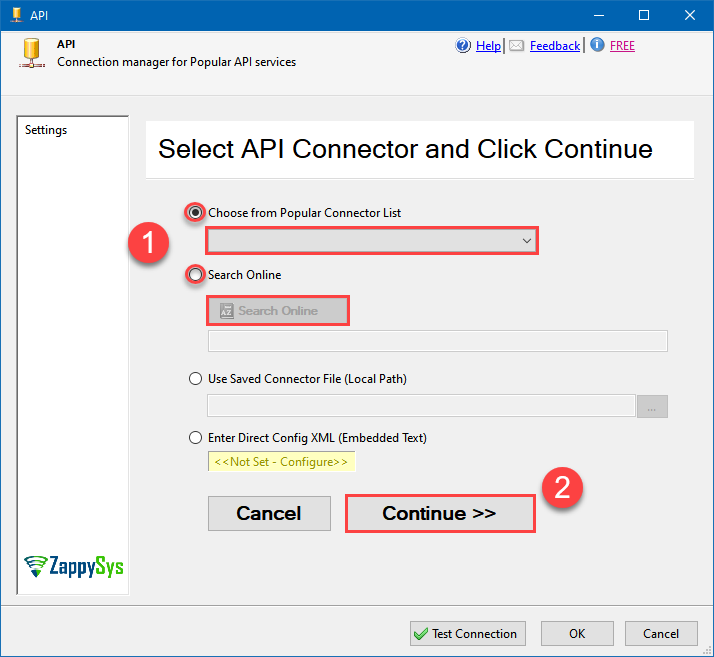
-
Select your authentication scenario below to expand connection configuration steps to:
- Configure the authentication in OneDrive.
- Enter those details into the API Connection Manager configuration.
OneDrive authentication
Use delegated access (User Credentials) whenever you want to let a signed-in user work with their own resources or resources they can access. Whether it's an admin setting up policies for their entire organization or a user deleting an email in their inbox, all scenarios involving user actions should use delegated access. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with delegated access:
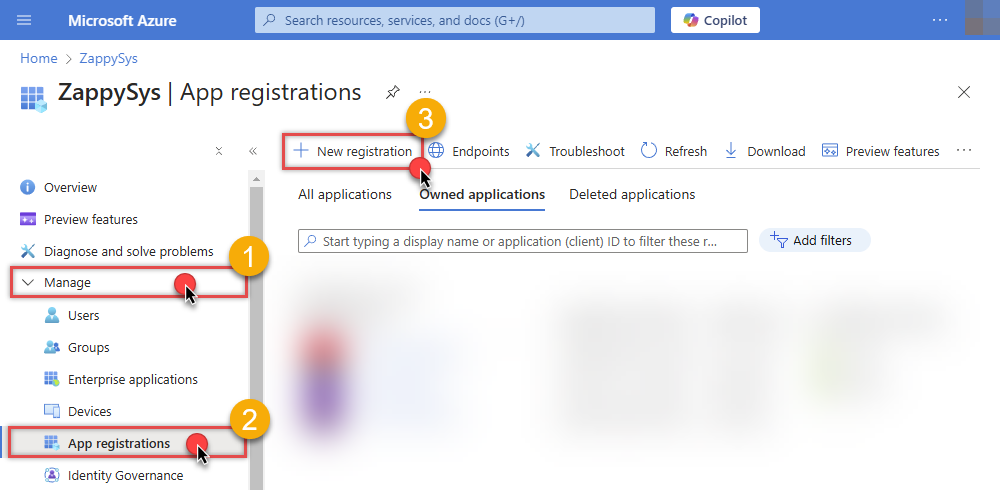
WARNING: To automate your company's processes, make sure you use a system/generic account (e.g.automation@my-company.com). When you use a personal account which is tied to a specific employee profile and that employee leaves the company, the token may become invalid and any automated processes using that token will start to fail.- Navigate to the Azure Portal and log in using your credentials.
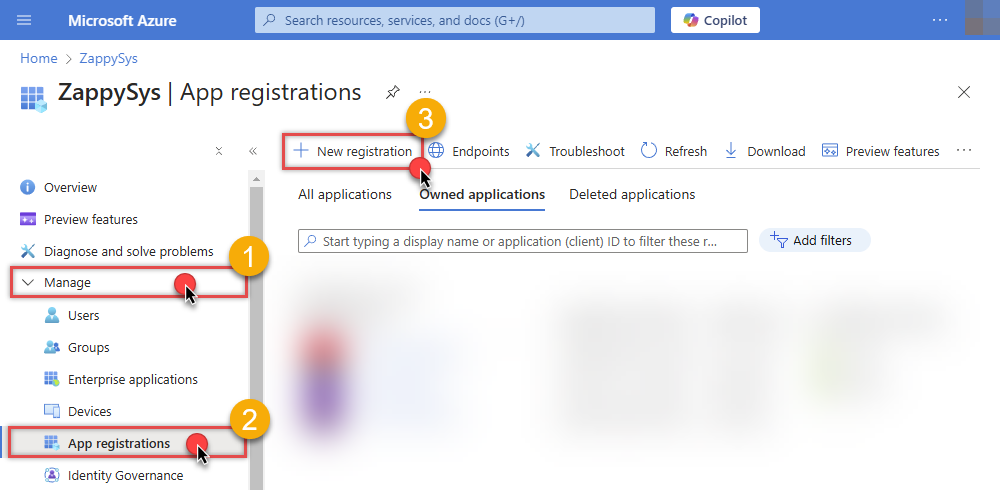
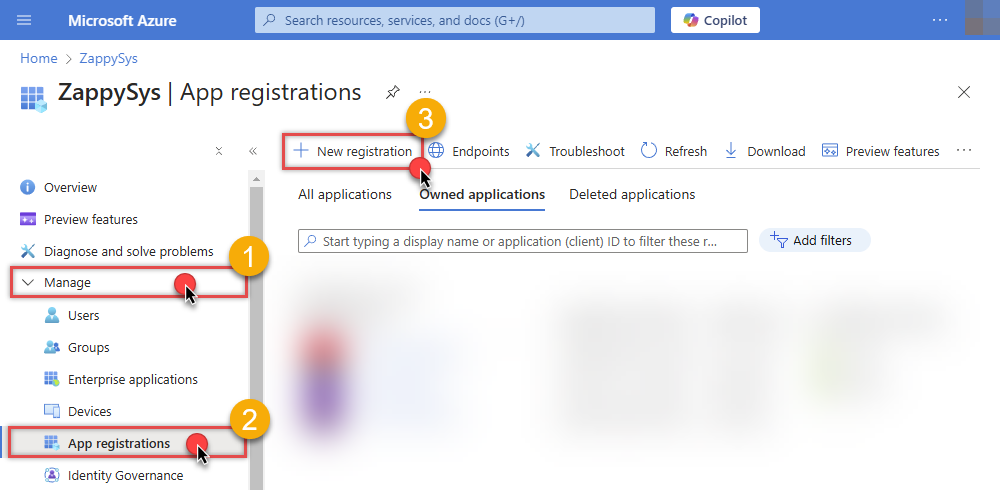
- Access Microsoft Entra ID.
-
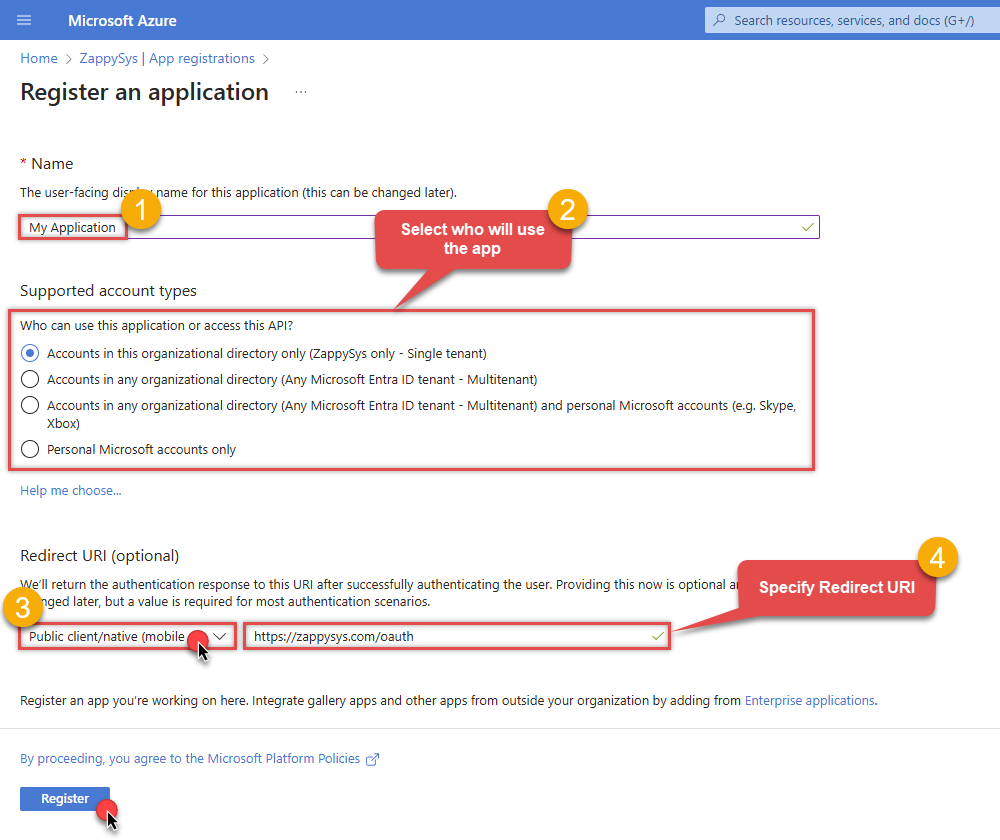
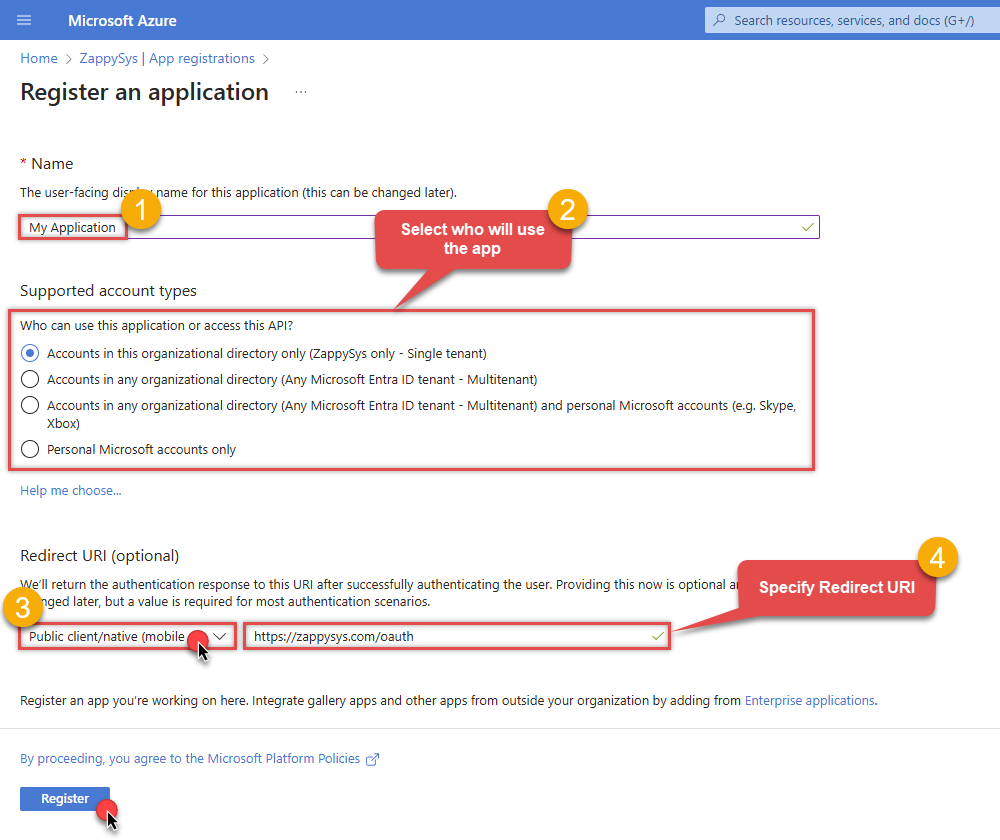
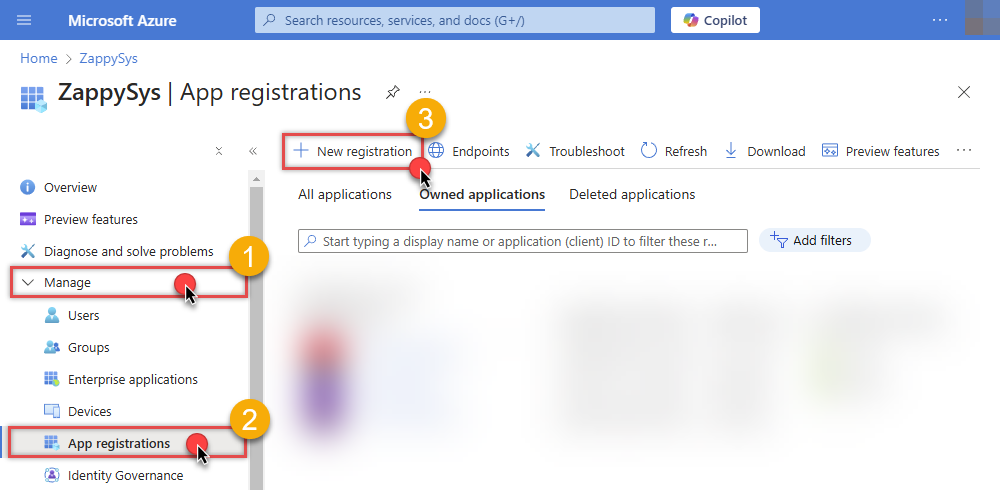
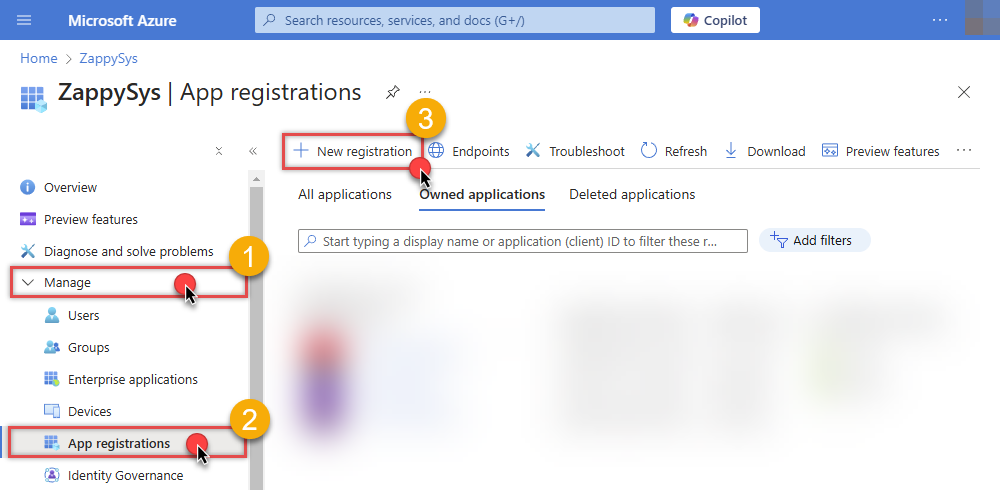
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
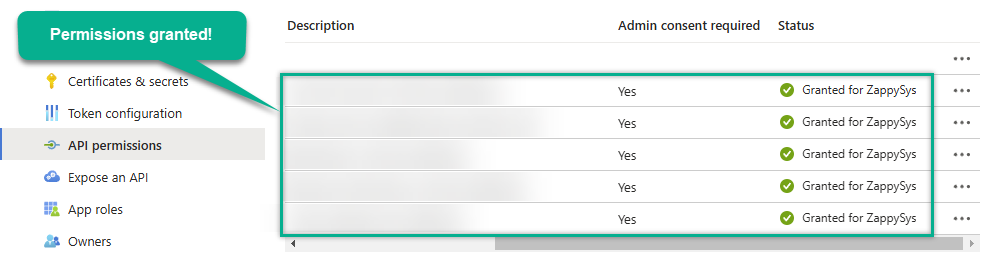
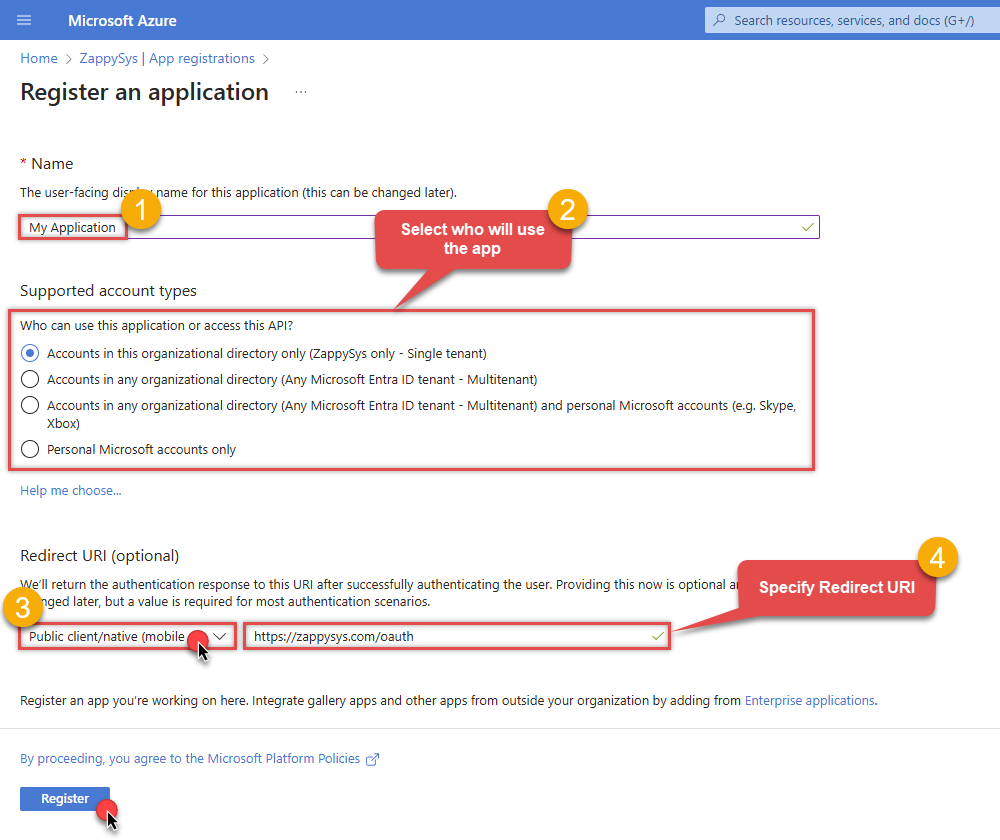
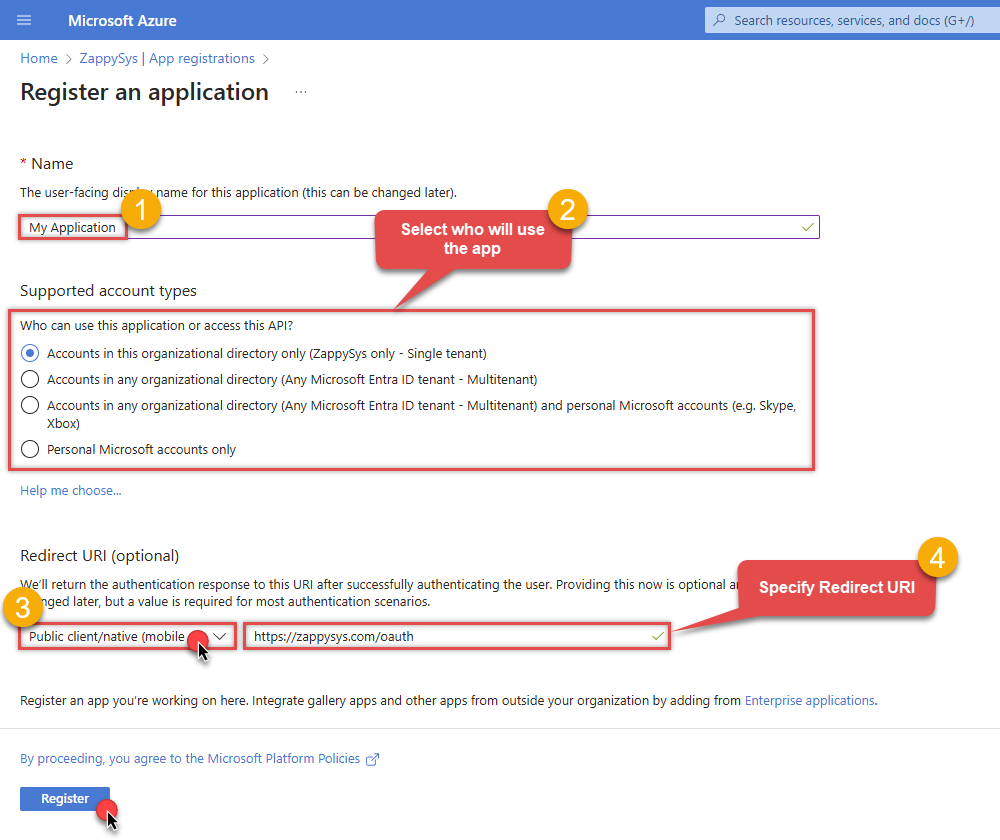
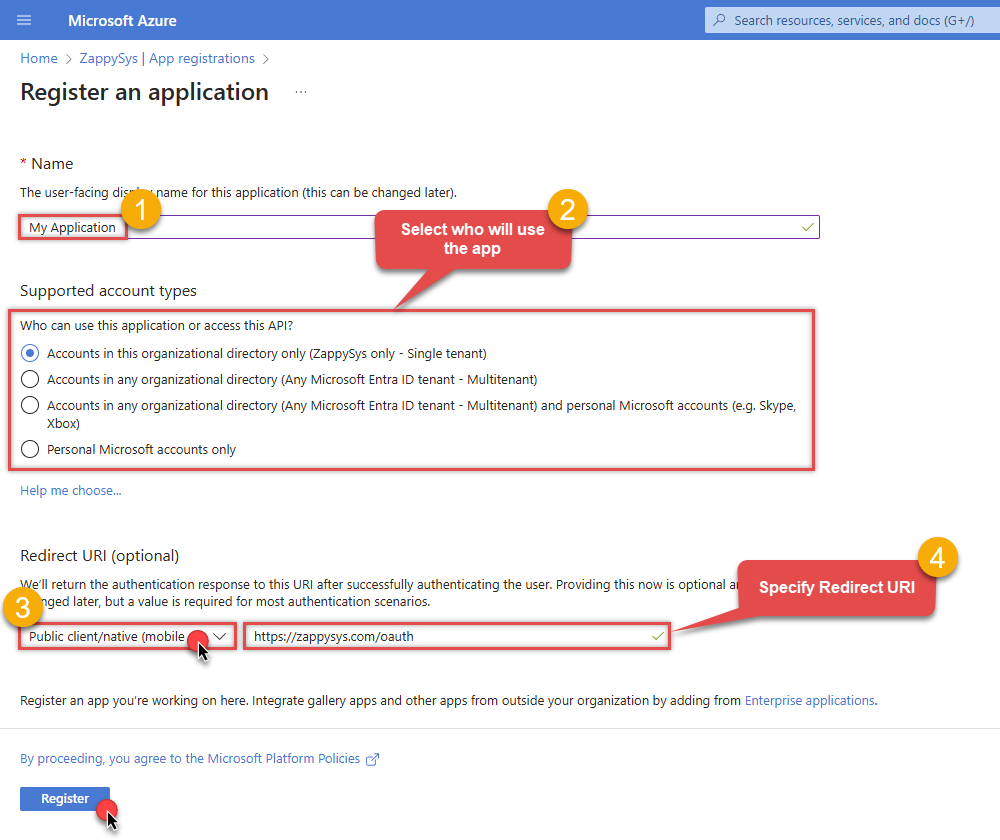
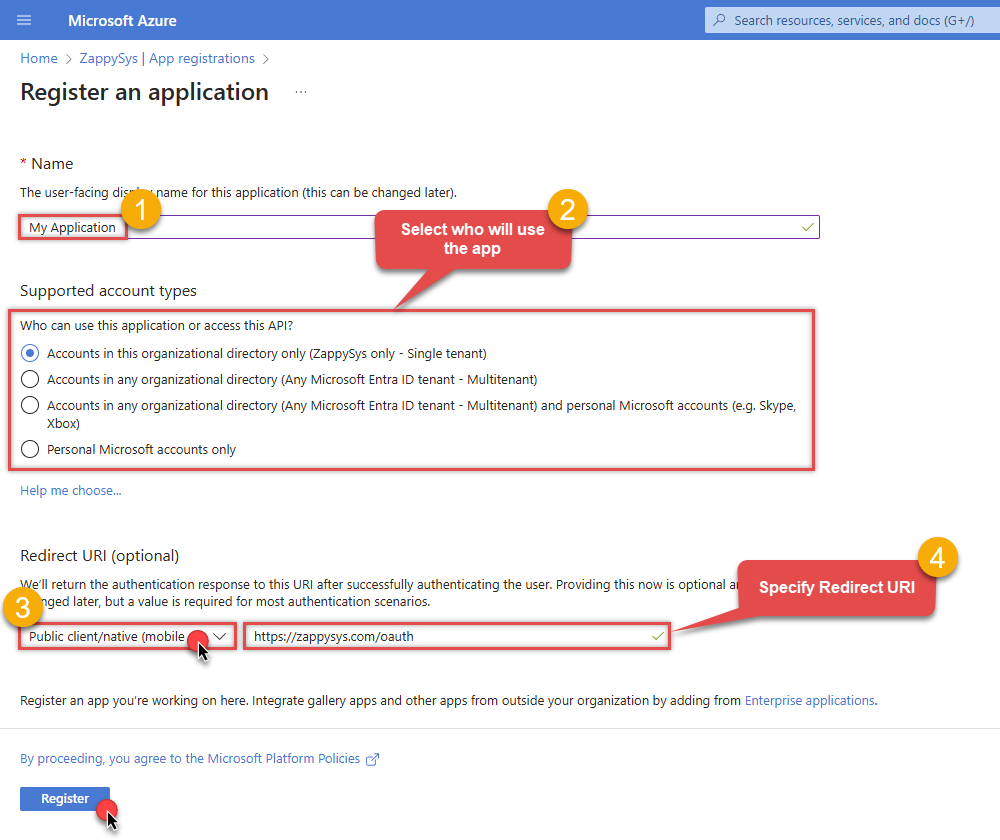
When configuration window opens, configure these fields:
-
Supported account type
- Use
Accounts in this organizational directory only, if you need access to data in your organization only.
- Use
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Use
https://zappysys.com/oauthas the URL.
- Set the type to
-
Supported account type
-
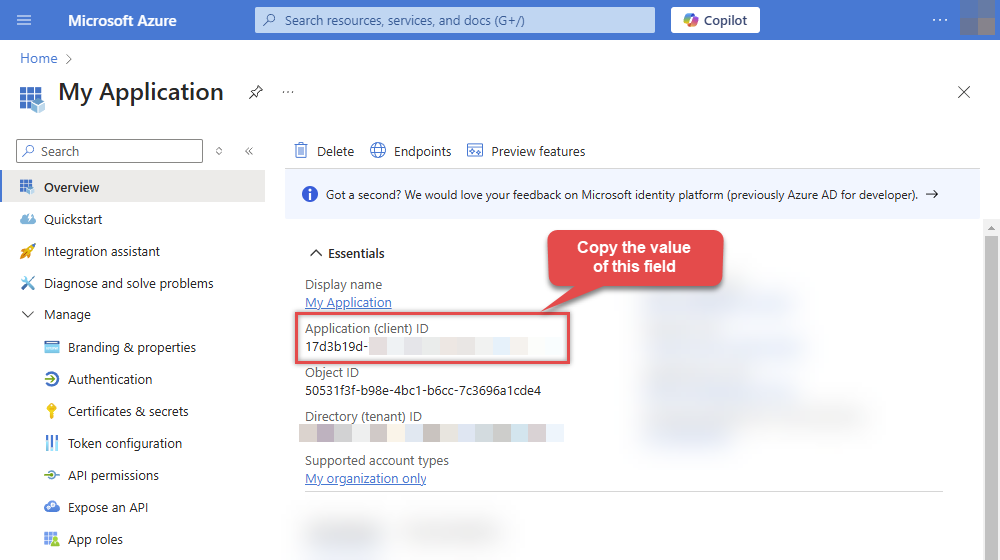
After registering the app, copy the Application (client) ID for later:
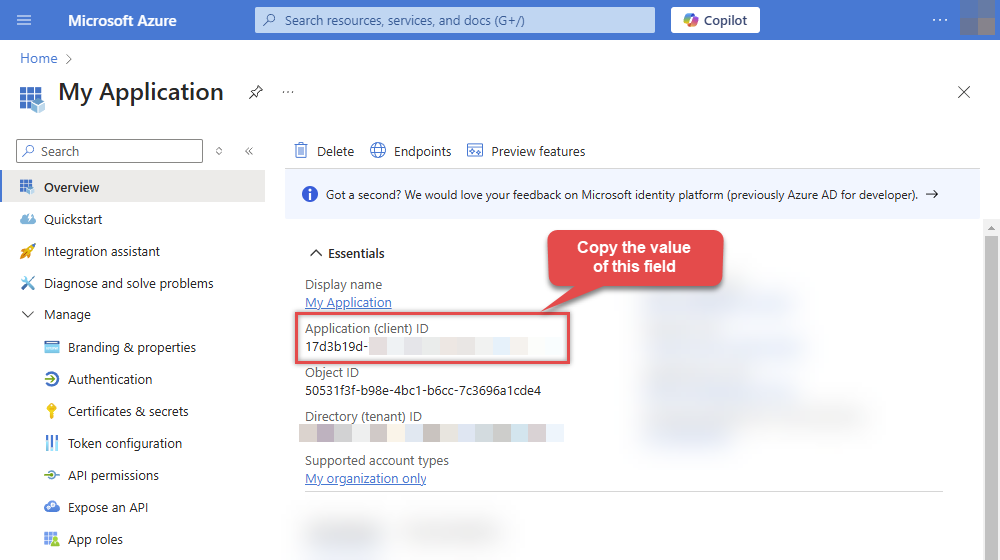
-
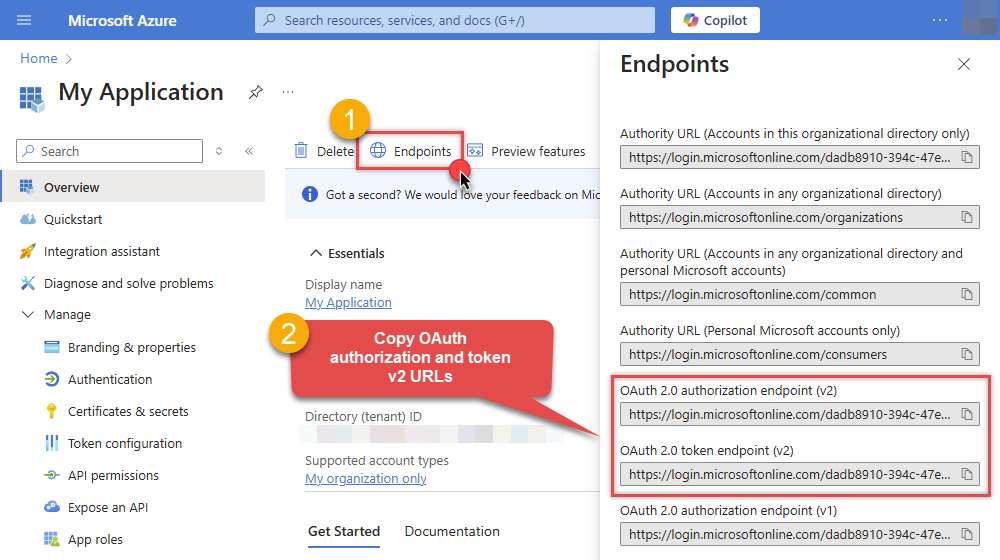
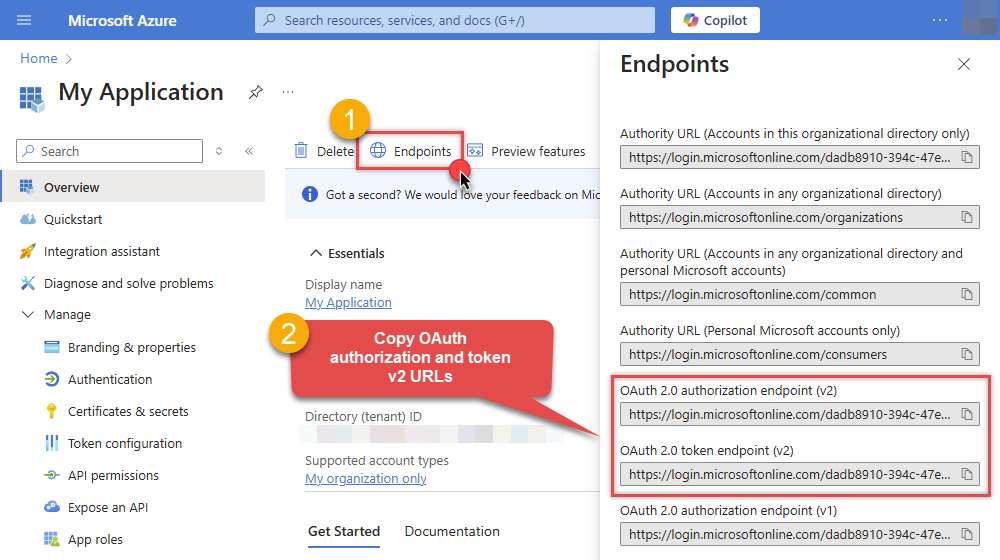
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs to use later in the configuration:
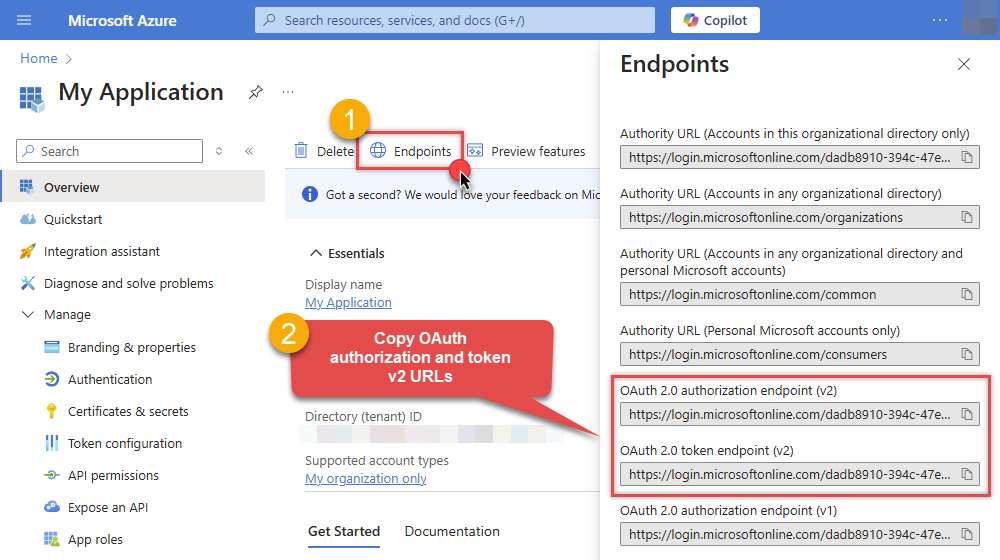
-
Now go to SSIS package or ODBC data source and use the copied values in User Credentials authentication configuration:
- In the Authorization URL field paste the OAuth authorization endpoint (v2) URL value you copied in the previous step.
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
-
In the Scope field use the default value or select individual scopes, e.g.:
-
email -
offline_access -
openid -
profile -
User.Read -
Files.Read.All -
Files.ReadWrite.All
-
- Press Generate Token button to generate Access and Refresh Tokens.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Now you are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
User Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
OneDriveUser Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Authorization URL Fill-in the parameter... Token URL Fill-in the parameter... Client ID Fill-in the parameter... Scope Fill-in the parameter... Optional Parameters Client Secret Refresh Token File Path Return URL https://zappysys.com/oauth Default Group or User Id (additional Scopes needed to list - If fails enter manually) Default Drive Id (Select after clicking **Generate Token**) me RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Login Prompt Option Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 0  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference.OneDrive authentication
Application-only access is broader and more powerful than delegated access (User Credentials), so you should only use app-only access where needed. Use it when: 1. The application needs to run in an automated way, without user input (for example, a daily script that checks emails from certain contacts and sends automated responses). 2. The application needs to access resources belonging to multiple different users (for example, a backup or data loss prevention app might need to retrieve messages from many different chat channels, each with different participants). 3. You find yourself tempted to store credentials locally and allow the app to sign in 'as' the user or admin. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Leave the URL field empty.
- Set the type to
-
After registering the app, copy the Application (client) ID for later:
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
-
Continue and create Client secret:
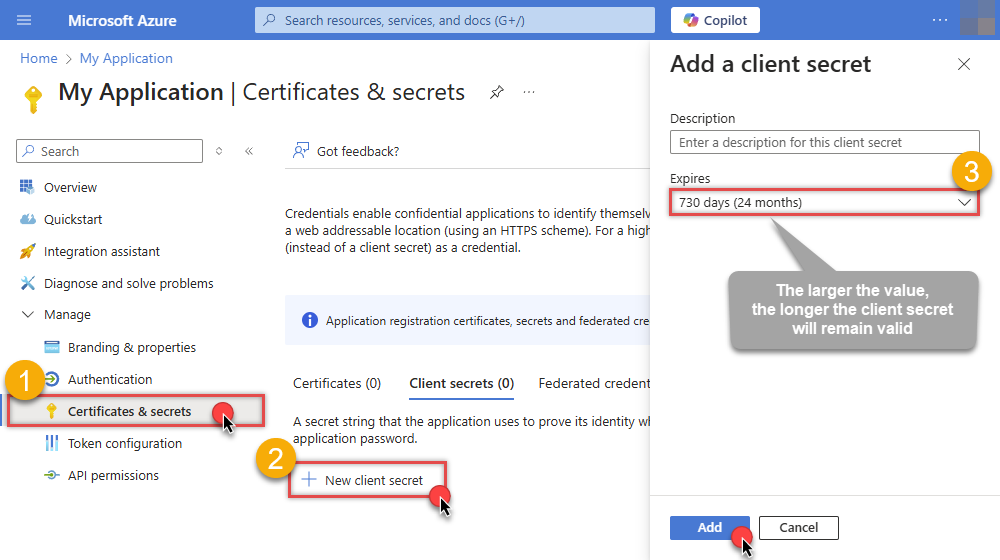
-
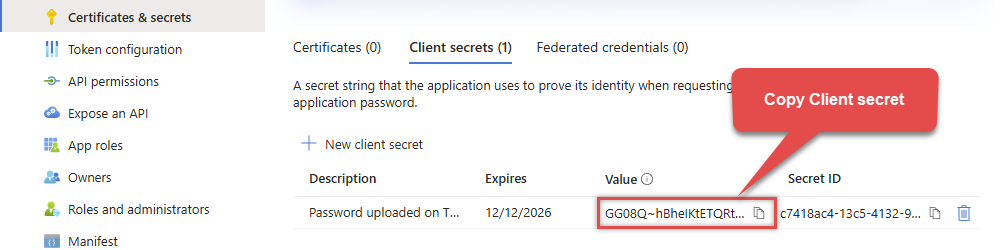
Then copy the Client secret for later steps:
-
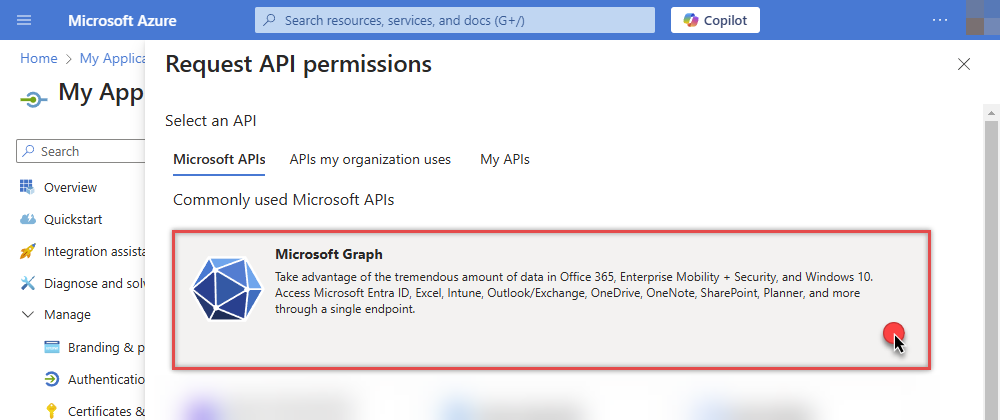
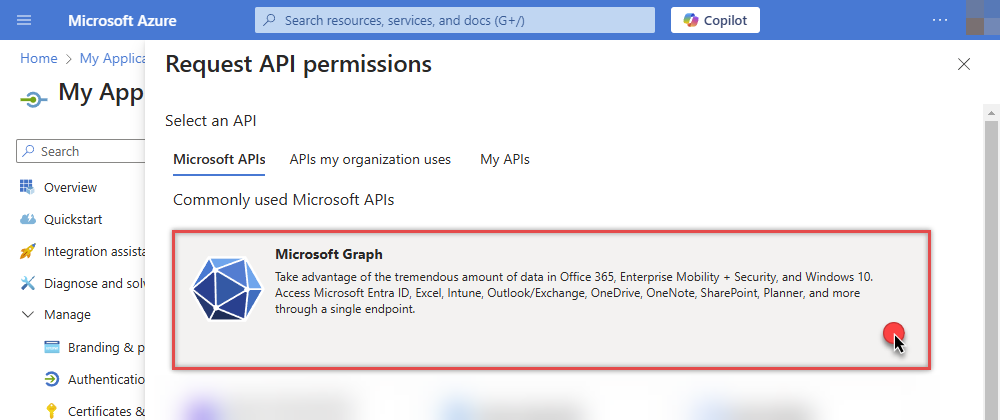
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
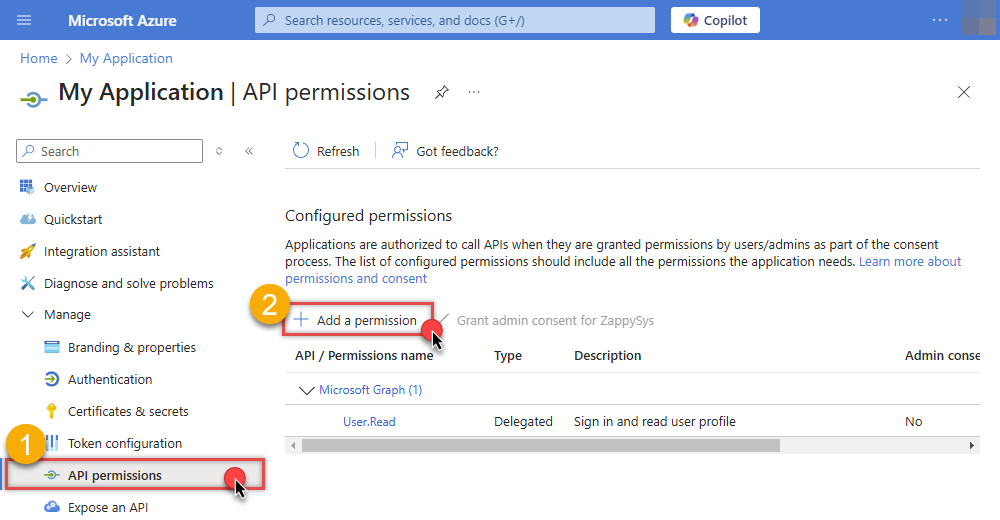
-
Select Microsoft Graph:
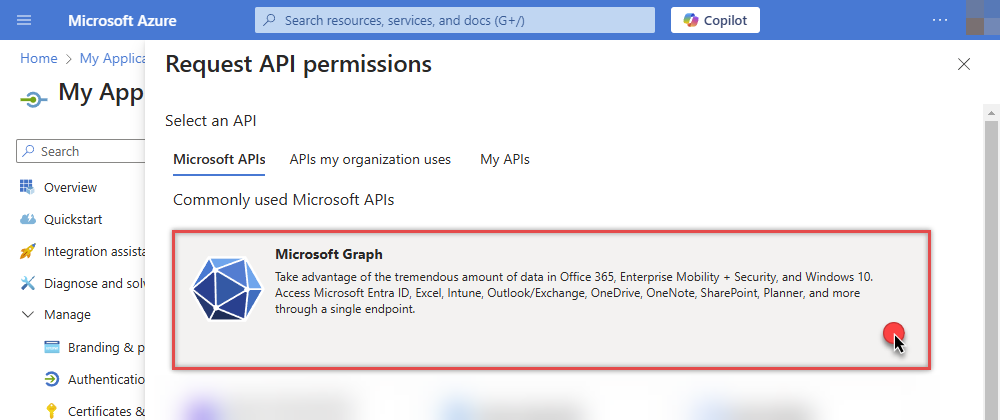
-
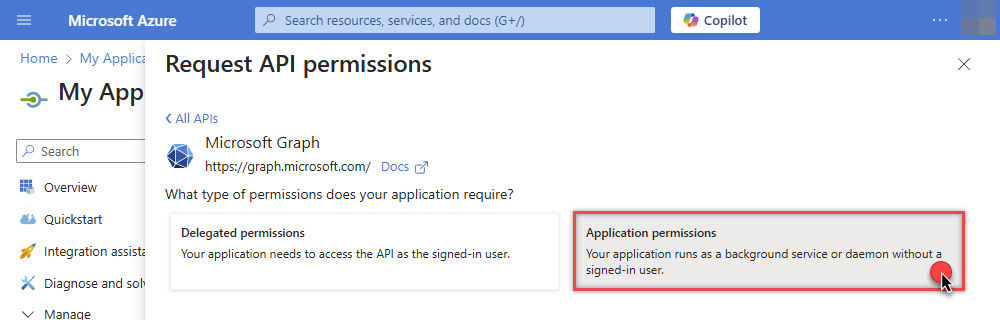
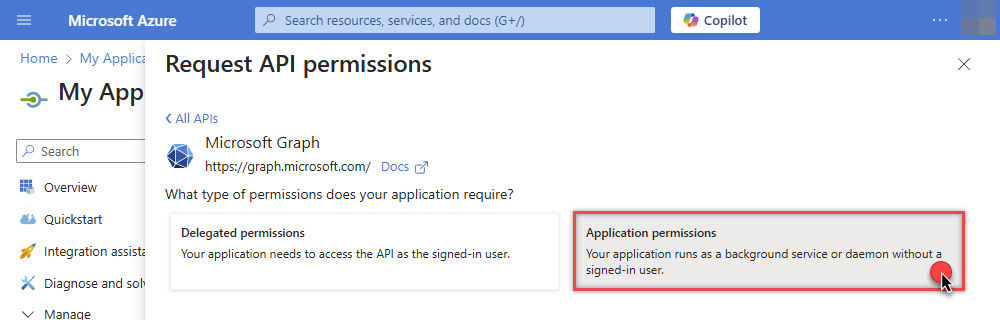
Then choose Application permissions option:
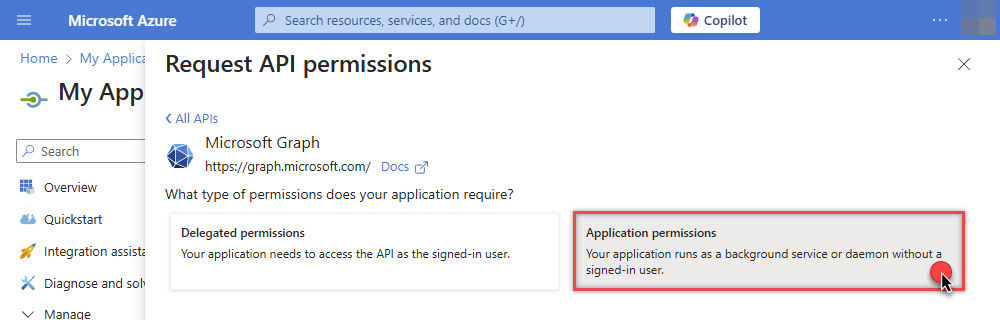
-
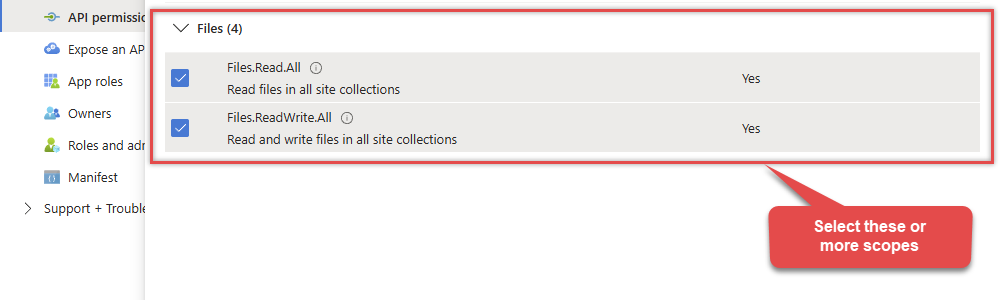
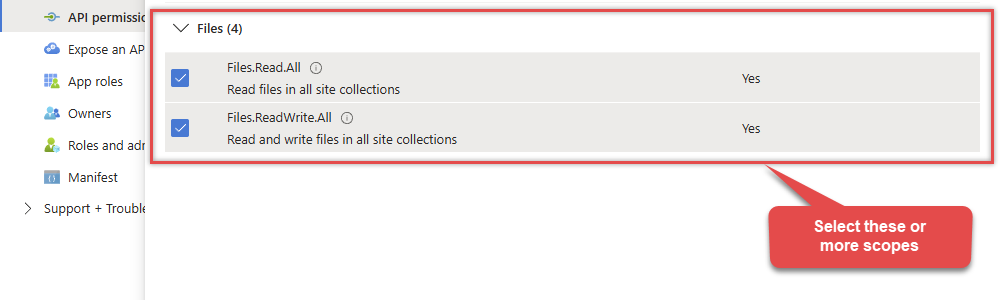
Continue by adding these Files (OneDrive) permissions (Just search for "Files" and then select desired permissions):
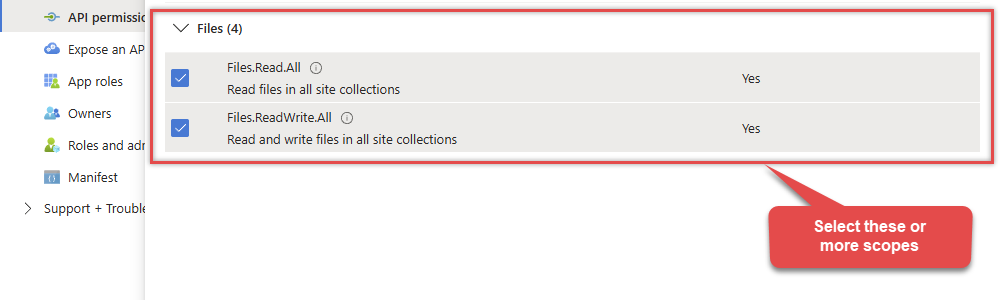
-
Finish by clicking Add permissions button:

-
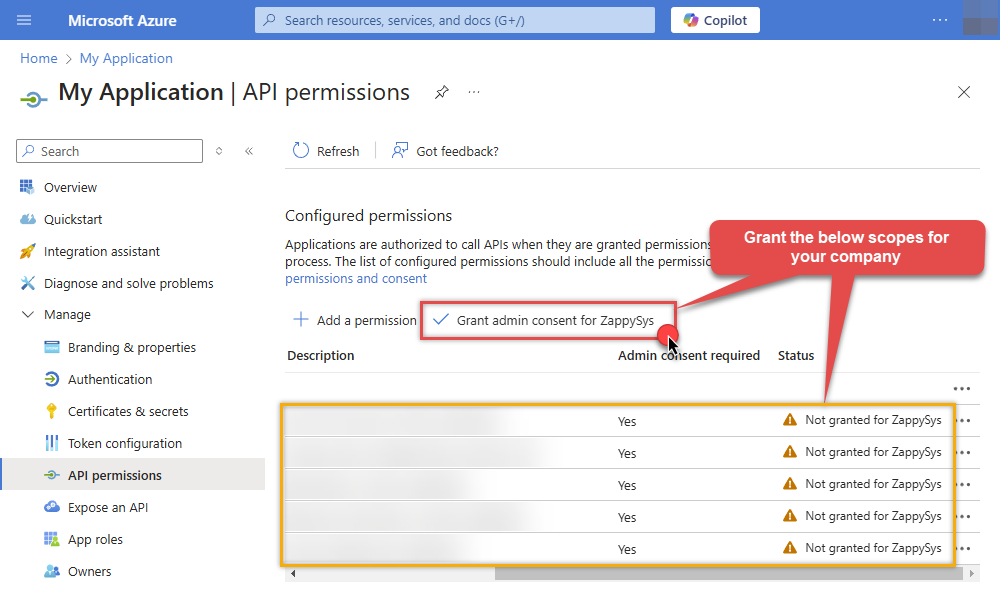
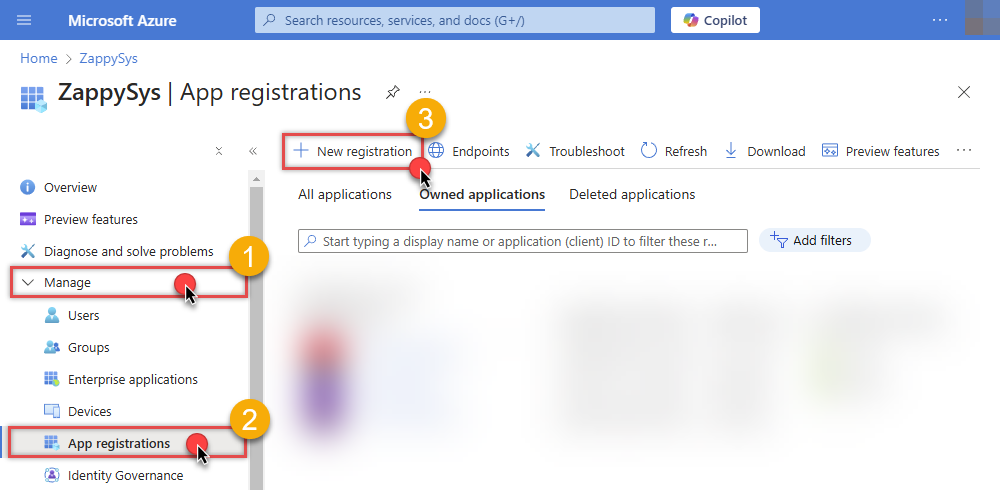
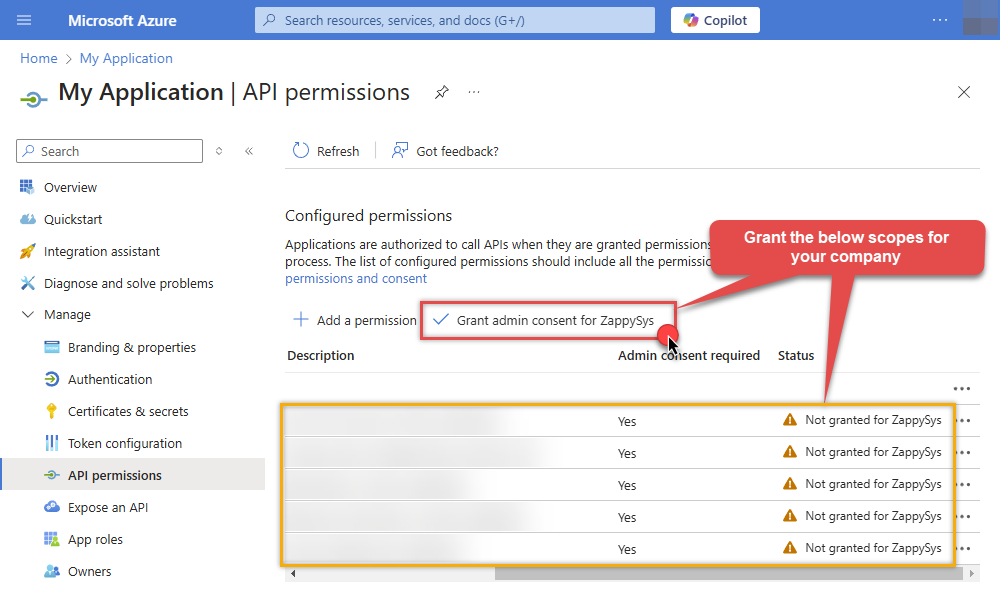
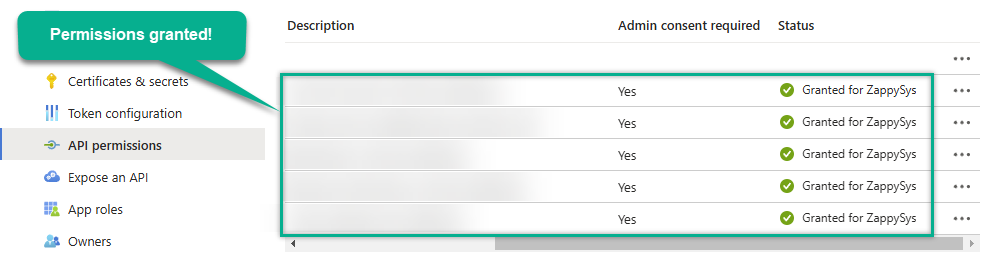
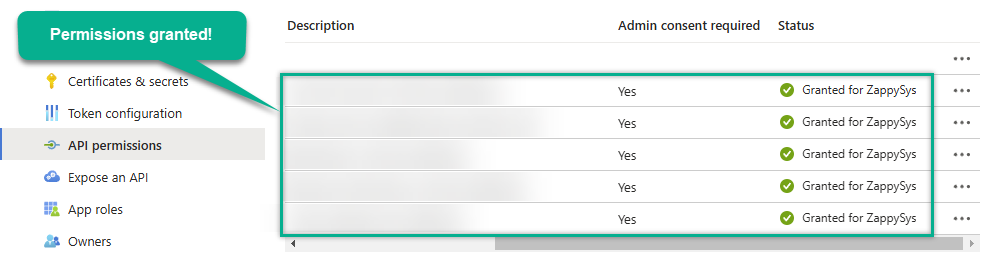
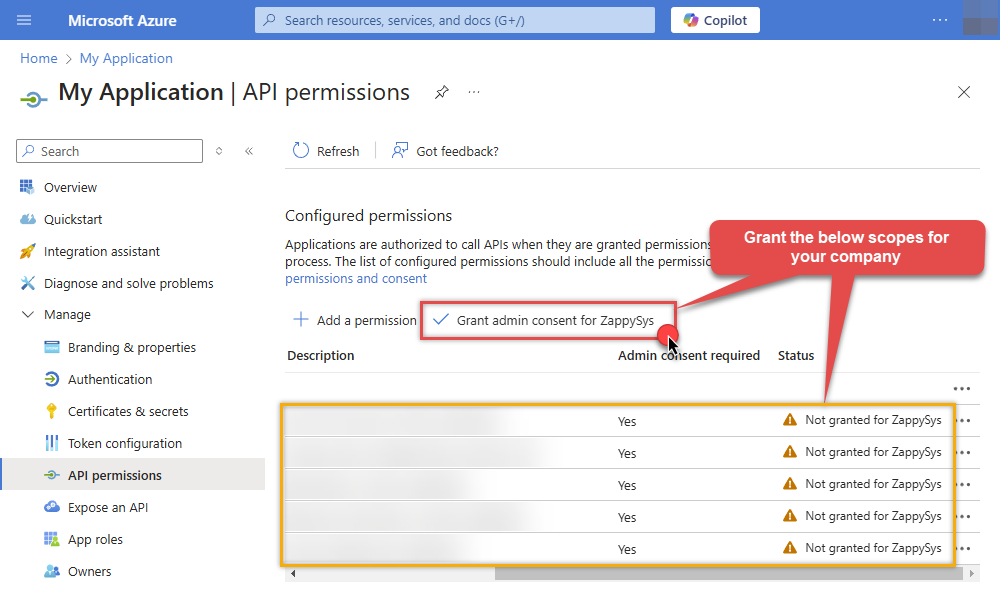
Now it's time to Grant admin consent for your application:
-
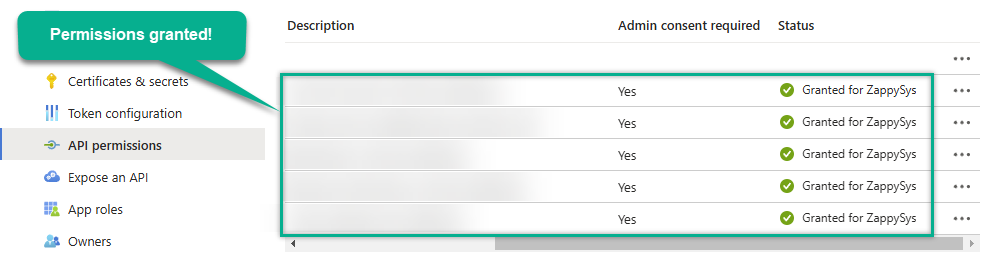
Confirm all the permissions are granted:
-
Now go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- In the Client Secret field paste the Client secret value you copied in the previous step.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Application Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
OneDriveApplication Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Client Secret Fill-in the parameter... Default Group or User Id (additional Scopes needed to list - If fails enter manually) Fill-in the parameter... Default Drive Id Fill-in the parameter... Optional Parameters Scope https://graph.microsoft.com/.default RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference.OneDrive authentication
Similar to Assplication-only access but with JWT sign with Private Key [API reference]
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
After registering the app, copy the Application (client) ID for later:
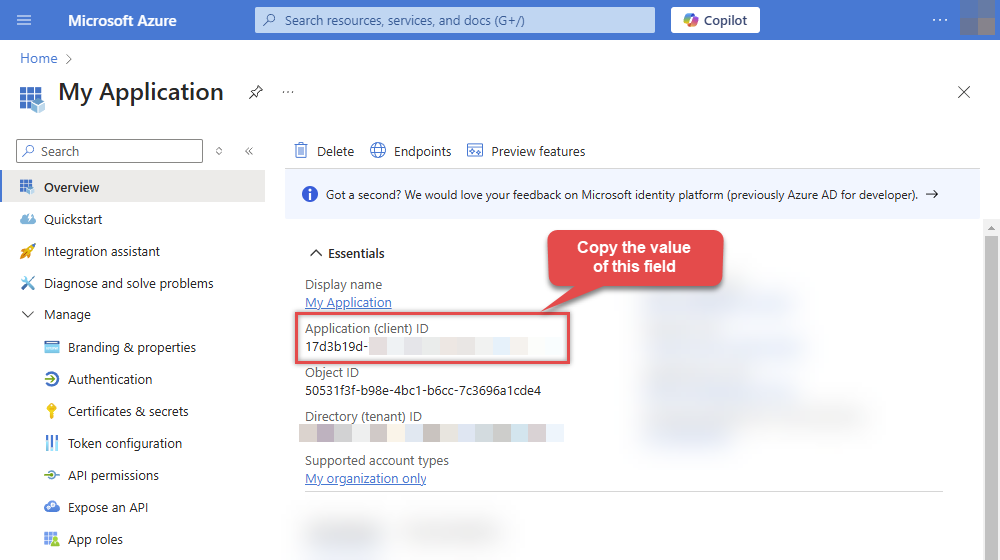
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
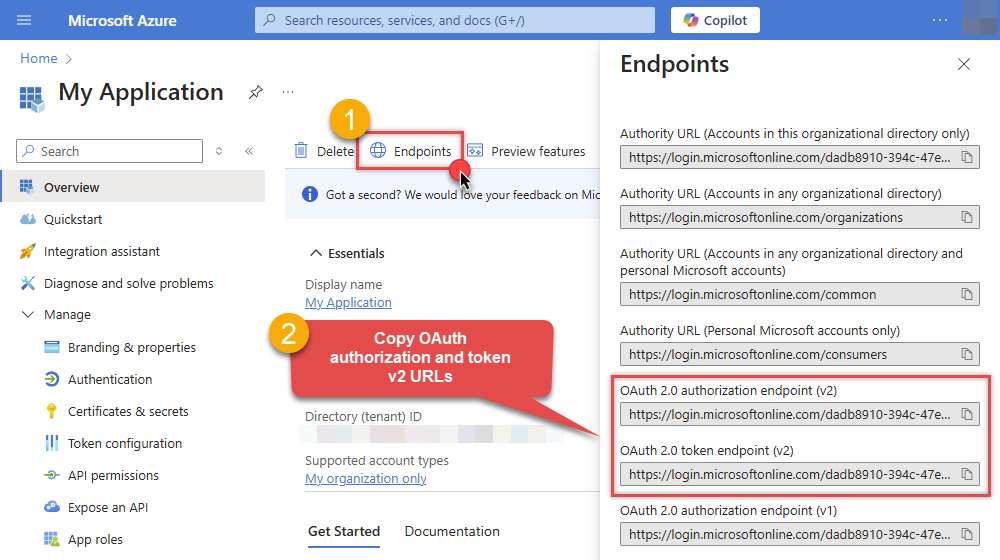
Configure App Permissions
-
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
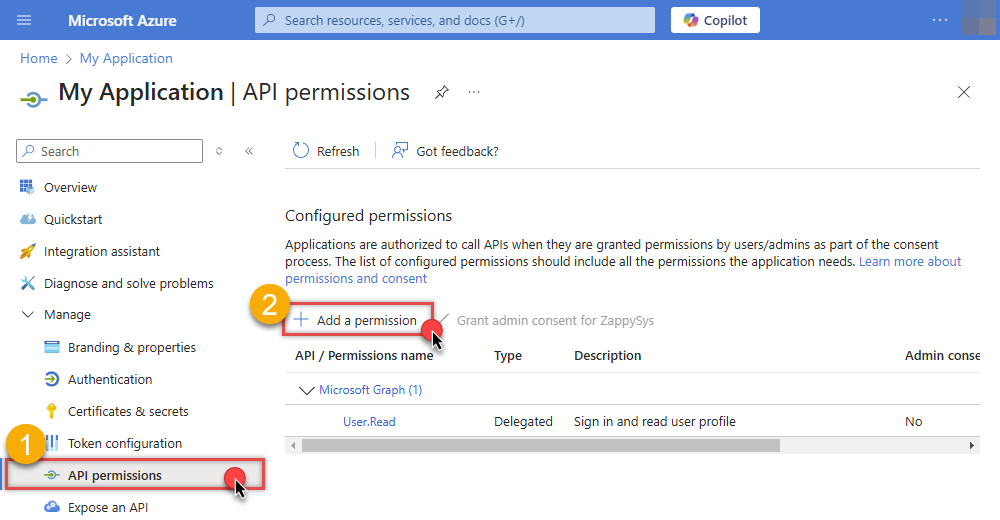
-
Select Microsoft Graph:
-
Then choose Application permissions option:
-
Continue by adding these Files (OneDrive) permissions (Just search for "Files" and then select desired permissions):
-
Finish by clicking Add permissions button:

-
Now it's time to Grant admin consent for your application:
-
Confirm all the permissions are granted:
Generate a Self-Signed Certificate
Now let's go through setting up a certificate-based authentication flow for Microsoft Graph or other Azure AD protected APIs using client credentials and a JWT.
You can use OpenSSL or any other way to generate Certificate file but to make it simple we will use below example PowerShell script.
Open PowerShell and execute code listed in below steps.
# Run this in PowerShell #Change .AddYears(1) to desired number. By default it expires certificate in one year as per below code. $cert = New-SelfSignedCertificate ` -Subject "CN=MyClientAppCert" ` -KeySpec Signature ` -KeyExportPolicy Exportable ` -KeyLength 2048 ` -CertStoreLocation "Cert:\CurrentUser\My" ` -KeyAlgorithm RSA ` -HashAlgorithm SHA256 ` -NotAfter (Get-Date).AddYears(1) ` -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider" # Export private key (.pfx) - Keep this with you to make API calls (SECRET KEY - DONOT SHARE) $pfxPath = "$env:USERPROFILE\Desktop\private_key.pfx" $pwd = ConvertTo-SecureString -String "yourStrongPassword123" -Force -AsPlainText Export-PfxCertificate -Cert $cert -FilePath $pfxPath -Password $pwd # Export public certificate (.cer) - UPLOAD this to Azure Portal $cerPath = "$env:USERPROFILE\Desktop\public_key.cer" Export-Certificate -Cert $cert -FilePath $cerPathUpload the Certificate (i.e. Public Key *.cer)
Once we have certificate file generated.- In your App Registration, go to Certificates & secrets
- Under Certificates, click Upload certificate
- Select the
.cerfile (public certificate)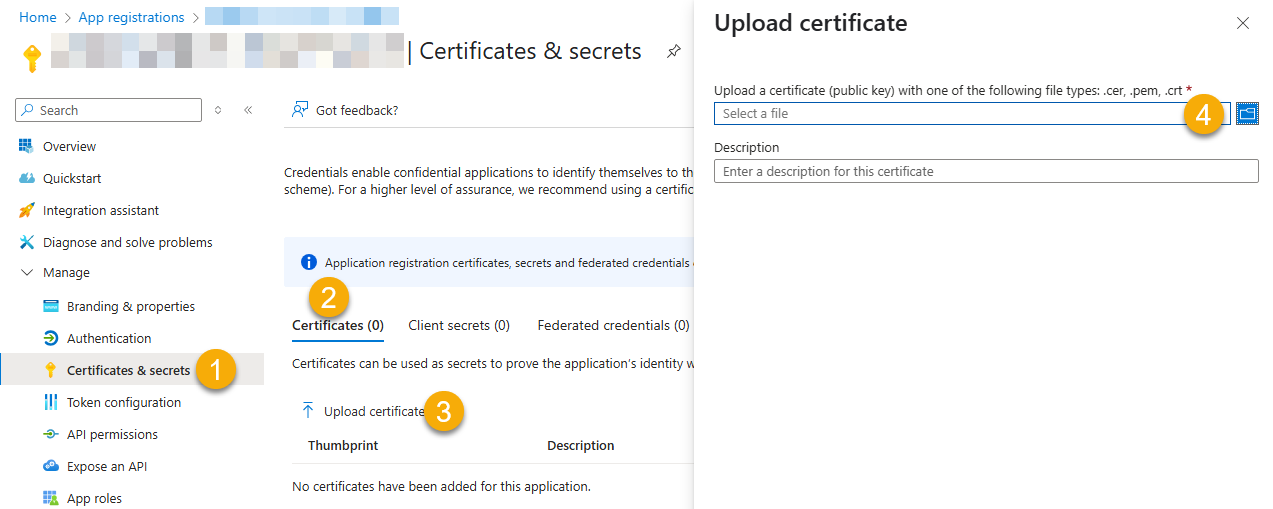
- Click Select a file (Browse button)
- Select public key file (*.cer) from local machine and click OK to upload
Configure ZappySys Connection - Use private key (i.e. *.pfx or *.pem)
Now its time to use certificate pfx file (private key) generated in the previous step (NOTE: PFX file contains both private key and public key).-
Go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- Configure private key
- go to Certificate Tab
- Change Storage Mode to
Disk File: *.pfx format (PKCS#12).NOTE: You can also useStored In LocalMachinemode if PFX file already imported in the Local Certificate Storage Area - User Store OR Machine Store. If you used OpenSSL to generate key pair then useDisk File: *.pem format (PKCS#8 or PKCS#1)Mode for Cert Store Location. - Supply the key file path
- Supply the certificate password (same password used in earlier PowerShell script)
- Now go back to General Tab, choose Default Group / User Id and Default Drive Id from the drop down menu.
- Click Test connection see everything is good
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Application Credentials with Certificate (Sign JWT with Private Key) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
OneDriveApplication Credentials with Certificate (Sign JWT with Private Key) [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Certificate: *** Configure [Client Certificate] Tab *** Fill-in the parameter... Default Group or User Id (additional Scopes needed to list - If fails enter manually) Fill-in the parameter... Default Drive Id Fill-in the parameter... Optional Parameters RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference. -
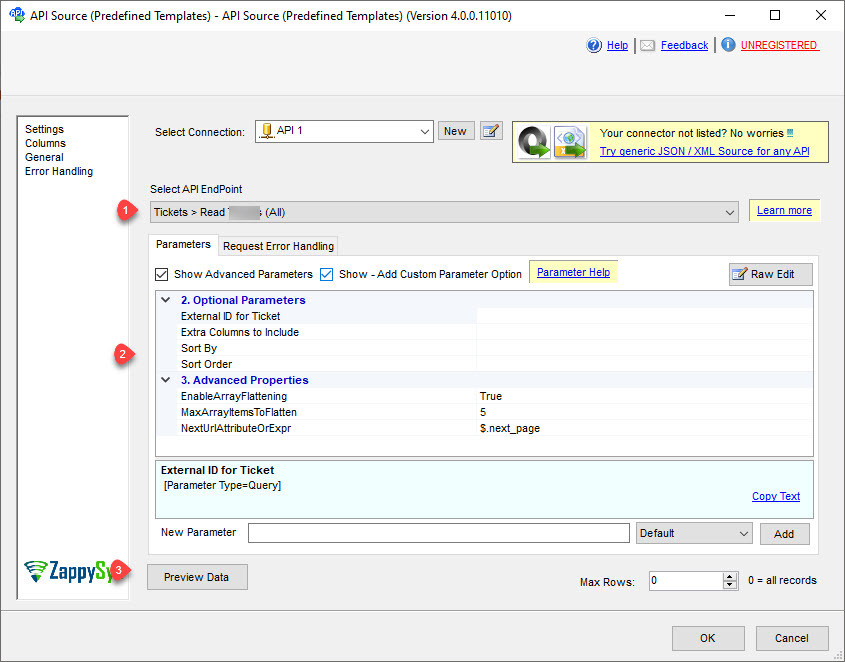
Select the desired endpoint, change/pass the properties values, and click on Preview Data button to make the API call.
API Source - OneDriveRead and write Microsoft OneDrive data effortlessly. Integrate, manage, and automate files and folders — almost no coding required.
-
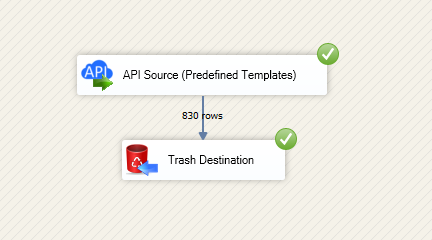
That's it! We are done! Just in a few clicks we configured the call to OneDrive using OneDrive Connector.
You can load the source data into your desired destination using the Upsert Destination , which supports SQL Server, PostgreSQL, and Amazon Redshift. We also offer other destinations such as CSV , Excel , Azure Table , Salesforce , and more . You can check out our SSIS PowerPack Tasks and components for more options. (*loaded in Trash Destination)
Write data to OneDrive using SSIS (Import data)
In this section we will learn how to configure and use OneDrive Connector in the API Destination to write data to OneDrive.
Video tutorial
This video covers following and more so watch carefully. After watching this video follow the steps described in this article.
- How to download SSIS PowerPack for OneDrive integration in SSIS
- How to configure connection for OneDrive
- How to write or lookup data to OneDrive
- Features about SSIS API Destination
- Using OneDrive Connector in SSIS
Step-by-step instructions
In upper section we learned how to read data, now in this section we will learn how to configure OneDrive in the API Source to POST data to the OneDrive.
-
Open Visual Studio and click Create a new project.
-
Select Integration Services Project. Enter a name and location for your project, then click OK.
-
From the SSIS Toolbox, drag and drop a Data Flow Task onto the Control Flow surface, and double-click it:

-
Make sure you are in the Data Flow Task designer:

-
Read the data from the source, using any desired source component. You can even make an API call using the ZappySys JSON/XML/API Source and read data from there. In this example, we will use an OLE DB Source component to read real-time data from a SQL Server database.
-
From the SSIS Toolbox drag and drop API Destination (Predefined Templates) on the Data Flow Designer surface and connect source component with it, and double click to edit it.

-
Select New Connection to create a new connection:
API Destination - OneDriveRead and write Microsoft OneDrive data effortlessly. Integrate, manage, and automate files and folders — almost no coding required.
-
To configure the OneDrive connector, choose one of the following methods:
- Choose from Popular Connector List: Select a pre-installed service directly from the dropdown menu.
- Search Online: Use this to find and download a new connector file to your computer.
- Use Saved/Downloaded File: Once the file is downloaded, browse your local drive to load it into the configuration.
After that, just click Continue >>:
OneDrive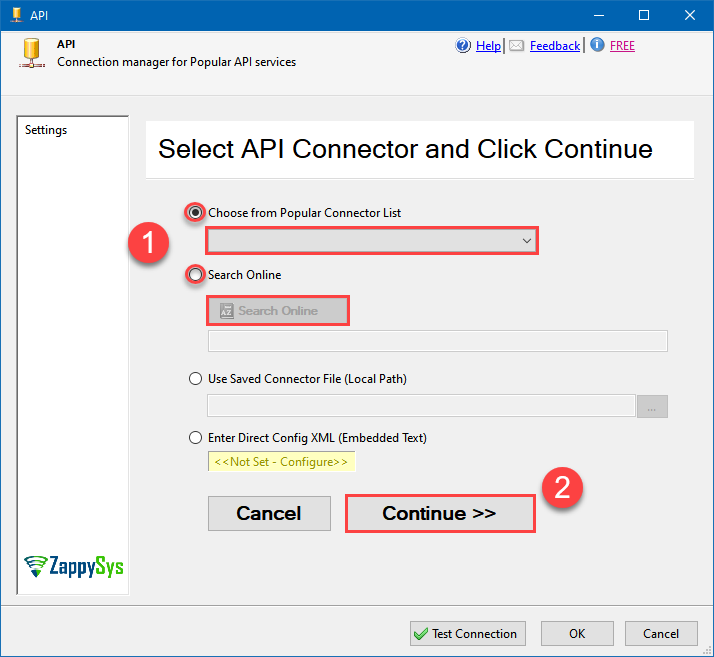
-
Proceed with selecting the desired Authentication Type. Then select API Base URL (in most cases default one is the right one). Finally, fill in all the required parameters and set optional parameters if needed. You may press a link Steps to Configure which will help set certain parameters. More info is available in Authentication section.
OneDrive authentication
Use delegated access (User Credentials) whenever you want to let a signed-in user work with their own resources or resources they can access. Whether it's an admin setting up policies for their entire organization or a user deleting an email in their inbox, all scenarios involving user actions should use delegated access. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with delegated access:
WARNING: To automate your company's processes, make sure you use a system/generic account (e.g.automation@my-company.com). When you use a personal account which is tied to a specific employee profile and that employee leaves the company, the token may become invalid and any automated processes using that token will start to fail.- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- Use
Accounts in this organizational directory only, if you need access to data in your organization only.
- Use
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Use
https://zappysys.com/oauthas the URL.
- Set the type to
-
Supported account type
-
After registering the app, copy the Application (client) ID for later:
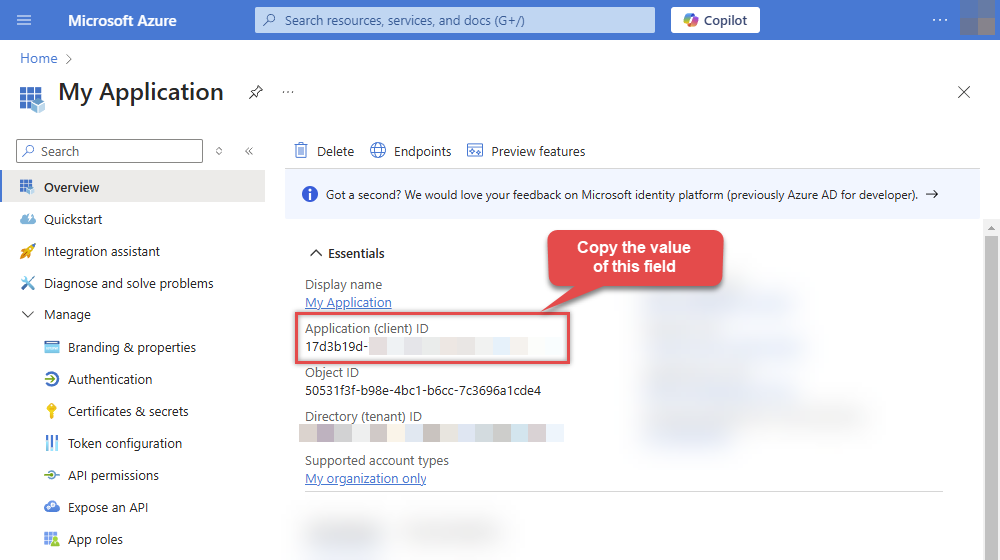
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs to use later in the configuration:
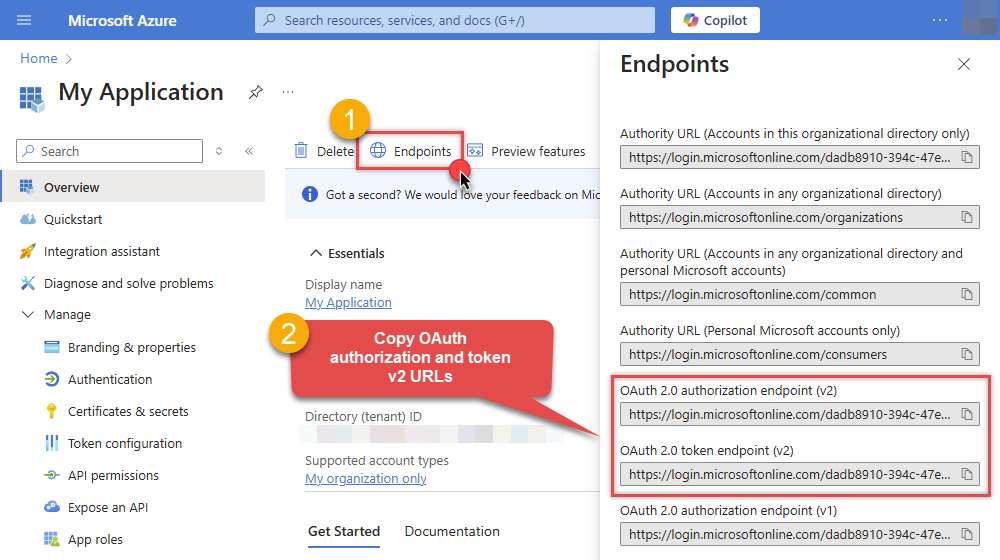
-
Now go to SSIS package or ODBC data source and use the copied values in User Credentials authentication configuration:
- In the Authorization URL field paste the OAuth authorization endpoint (v2) URL value you copied in the previous step.
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
-
In the Scope field use the default value or select individual scopes, e.g.:
-
email -
offline_access -
openid -
profile -
User.Read -
Files.Read.All -
Files.ReadWrite.All
-
- Press Generate Token button to generate Access and Refresh Tokens.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Now you are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
User Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
OneDriveUser Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Authorization URL Fill-in the parameter... Token URL Fill-in the parameter... Client ID Fill-in the parameter... Scope Fill-in the parameter... Optional Parameters Client Secret Refresh Token File Path Return URL https://zappysys.com/oauth Default Group or User Id (additional Scopes needed to list - If fails enter manually) Default Drive Id (Select after clicking **Generate Token**) me RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Login Prompt Option Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 0  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference.OneDrive authentication
Application-only access is broader and more powerful than delegated access (User Credentials), so you should only use app-only access where needed. Use it when: 1. The application needs to run in an automated way, without user input (for example, a daily script that checks emails from certain contacts and sends automated responses). 2. The application needs to access resources belonging to multiple different users (for example, a backup or data loss prevention app might need to retrieve messages from many different chat channels, each with different participants). 3. You find yourself tempted to store credentials locally and allow the app to sign in 'as' the user or admin. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Leave the URL field empty.
- Set the type to
-
After registering the app, copy the Application (client) ID for later:
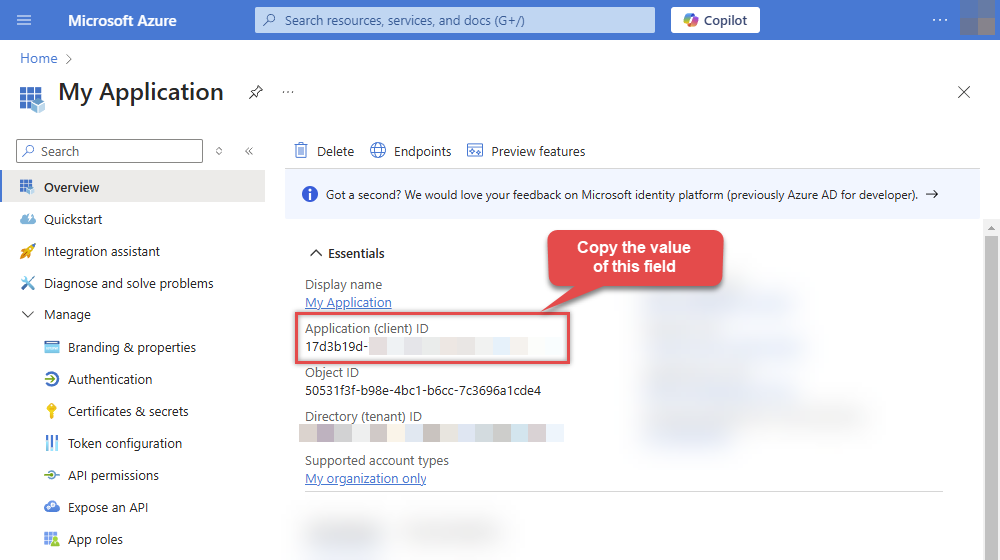
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
-
Continue and create Client secret:
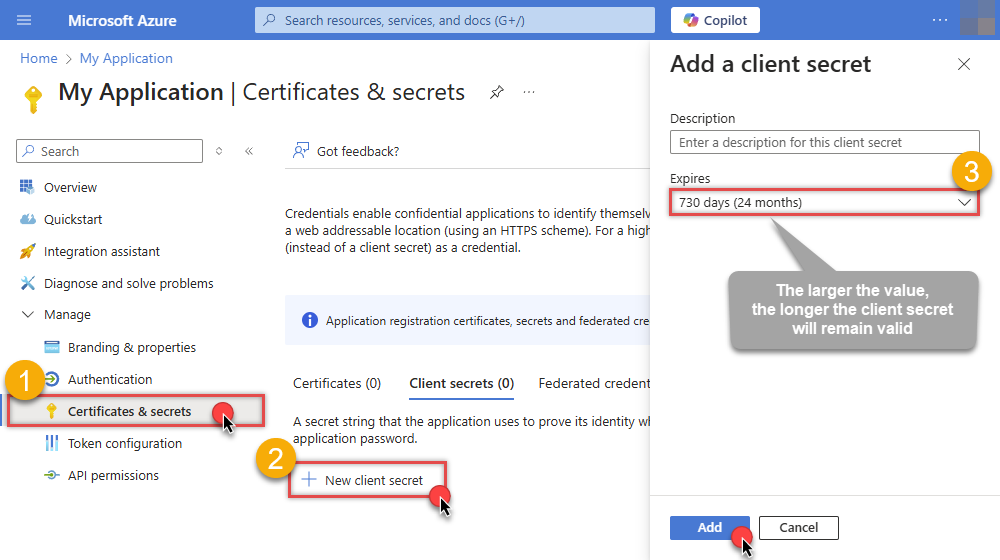
-
Then copy the Client secret for later steps:
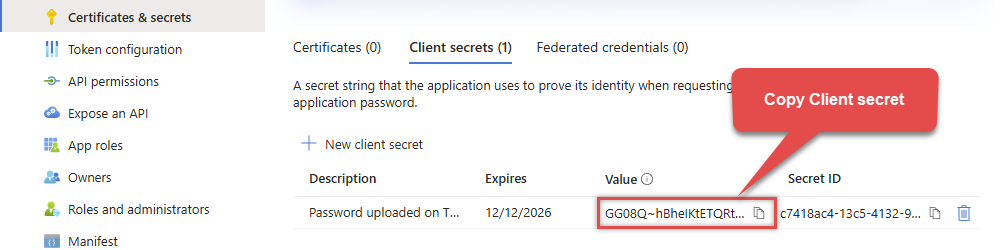
-
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
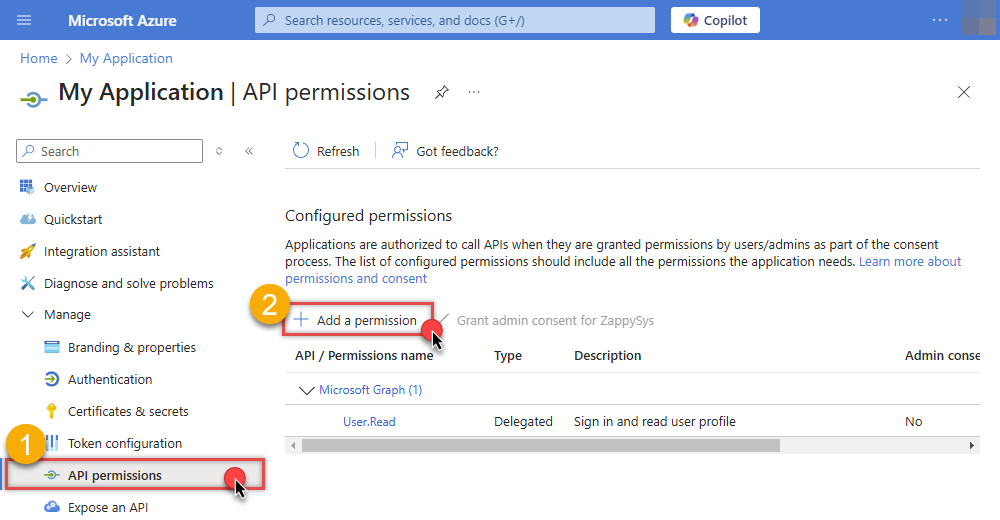
-
Select Microsoft Graph:
-
Then choose Application permissions option:
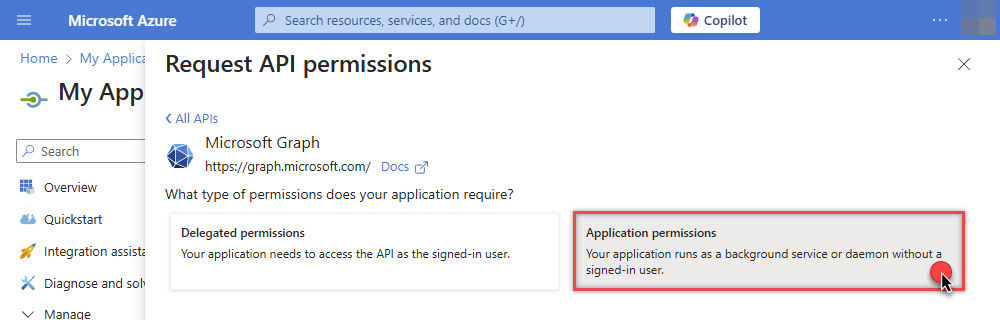
-
Continue by adding these Files (OneDrive) permissions (Just search for "Files" and then select desired permissions):
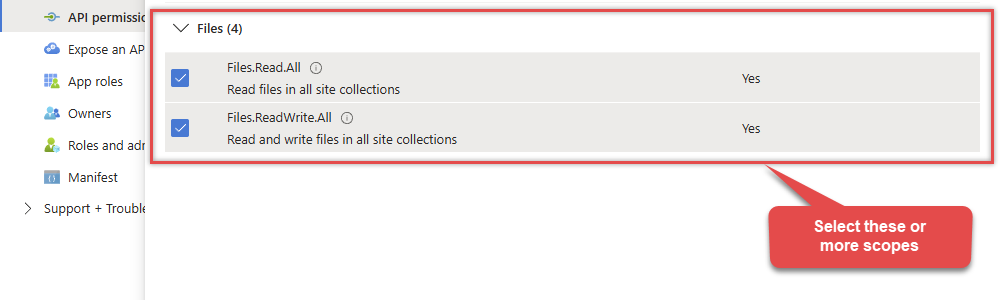
-
Finish by clicking Add permissions button:

-
Now it's time to Grant admin consent for your application:
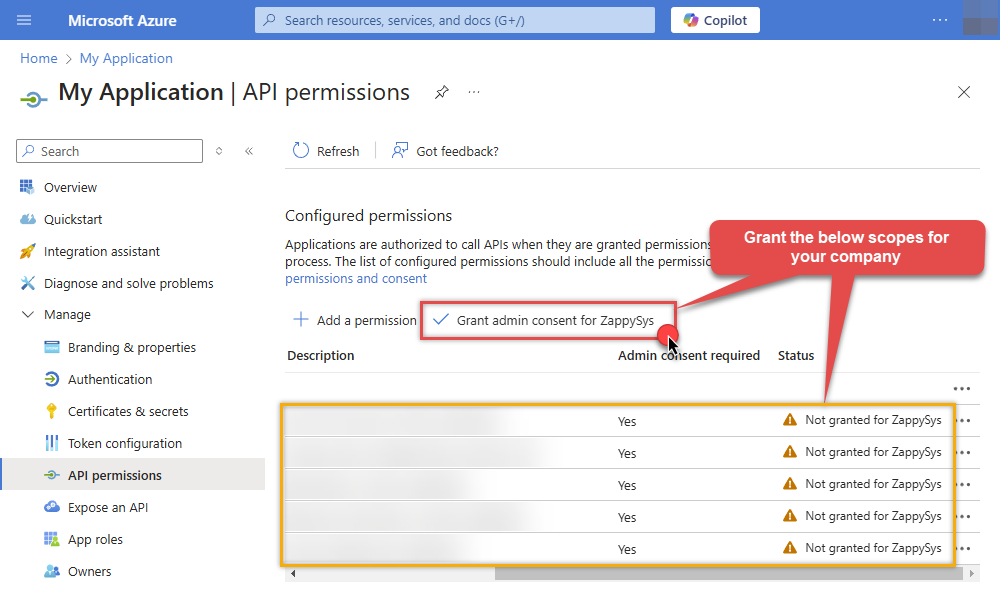
-
Confirm all the permissions are granted:
-
Now go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- In the Client Secret field paste the Client secret value you copied in the previous step.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Application Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
OneDriveApplication Credentials [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Client Secret Fill-in the parameter... Default Group or User Id (additional Scopes needed to list - If fails enter manually) Fill-in the parameter... Default Drive Id Fill-in the parameter... Optional Parameters Scope https://graph.microsoft.com/.default RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference.OneDrive authentication
Similar to Assplication-only access but with JWT sign with Private Key [API reference]
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
After registering the app, copy the Application (client) ID for later:
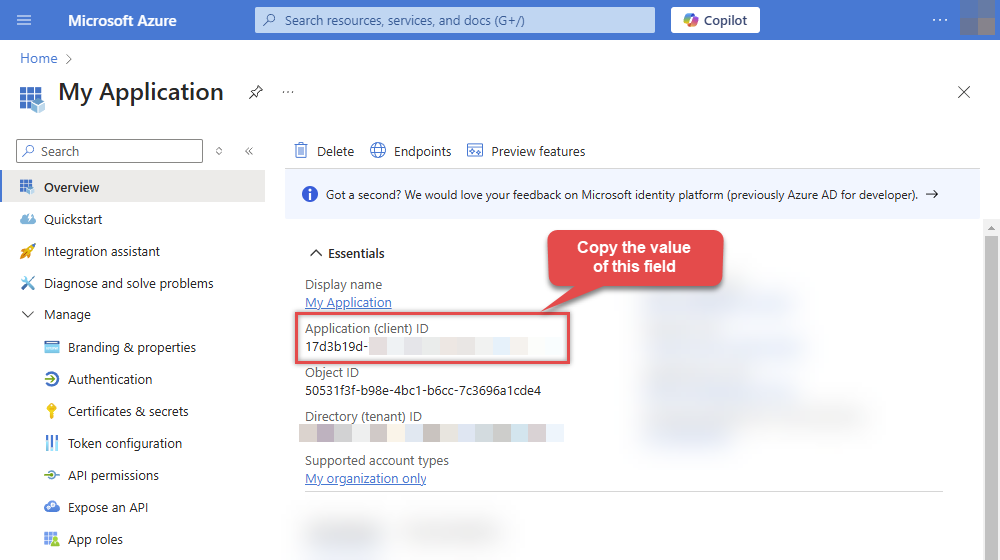
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
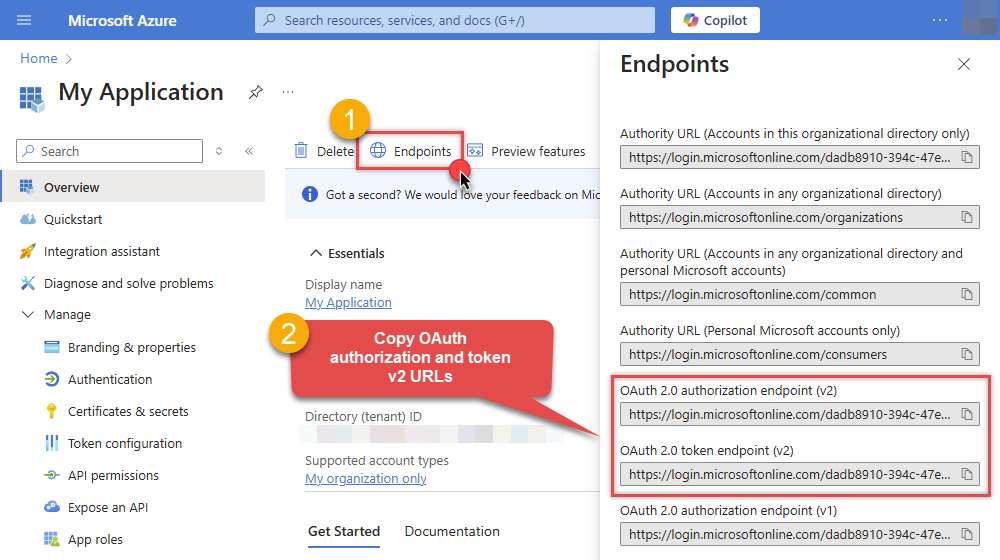
Configure App Permissions
-
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
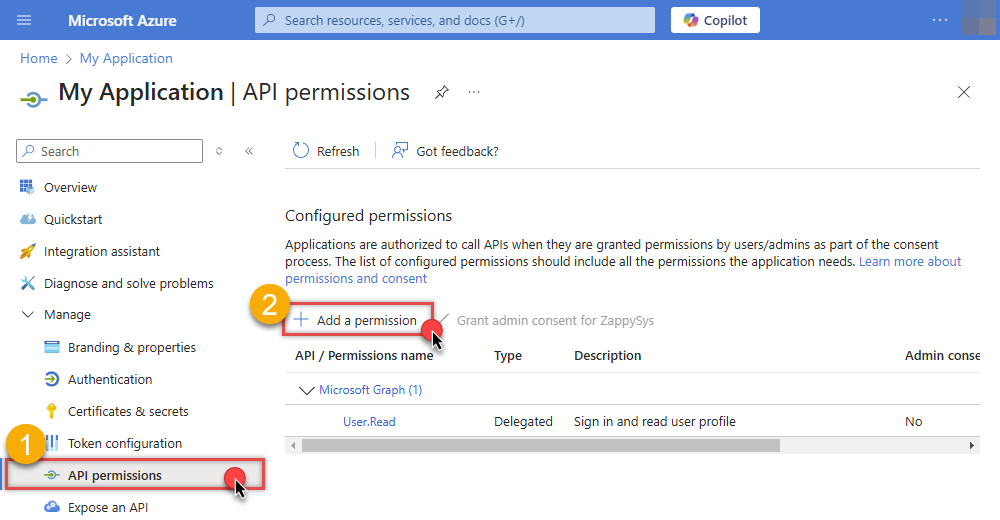
-
Select Microsoft Graph:
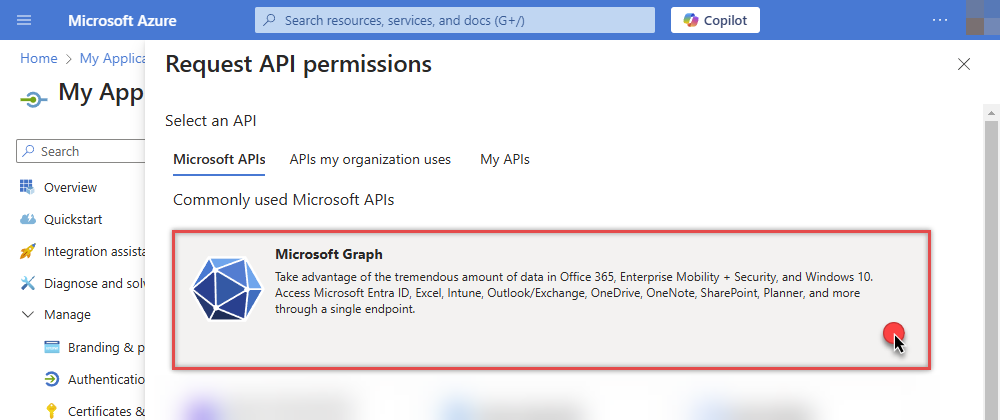
-
Then choose Application permissions option:
-
Continue by adding these Files (OneDrive) permissions (Just search for "Files" and then select desired permissions):
-
Finish by clicking Add permissions button:

-
Now it's time to Grant admin consent for your application:
-
Confirm all the permissions are granted:
Generate a Self-Signed Certificate
Now let's go through setting up a certificate-based authentication flow for Microsoft Graph or other Azure AD protected APIs using client credentials and a JWT.
You can use OpenSSL or any other way to generate Certificate file but to make it simple we will use below example PowerShell script.
Open PowerShell and execute code listed in below steps.
# Run this in PowerShell #Change .AddYears(1) to desired number. By default it expires certificate in one year as per below code. $cert = New-SelfSignedCertificate ` -Subject "CN=MyClientAppCert" ` -KeySpec Signature ` -KeyExportPolicy Exportable ` -KeyLength 2048 ` -CertStoreLocation "Cert:\CurrentUser\My" ` -KeyAlgorithm RSA ` -HashAlgorithm SHA256 ` -NotAfter (Get-Date).AddYears(1) ` -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider" # Export private key (.pfx) - Keep this with you to make API calls (SECRET KEY - DONOT SHARE) $pfxPath = "$env:USERPROFILE\Desktop\private_key.pfx" $pwd = ConvertTo-SecureString -String "yourStrongPassword123" -Force -AsPlainText Export-PfxCertificate -Cert $cert -FilePath $pfxPath -Password $pwd # Export public certificate (.cer) - UPLOAD this to Azure Portal $cerPath = "$env:USERPROFILE\Desktop\public_key.cer" Export-Certificate -Cert $cert -FilePath $cerPathUpload the Certificate (i.e. Public Key *.cer)
Once we have certificate file generated.- In your App Registration, go to Certificates & secrets
- Under Certificates, click Upload certificate
- Select the
.cerfile (public certificate)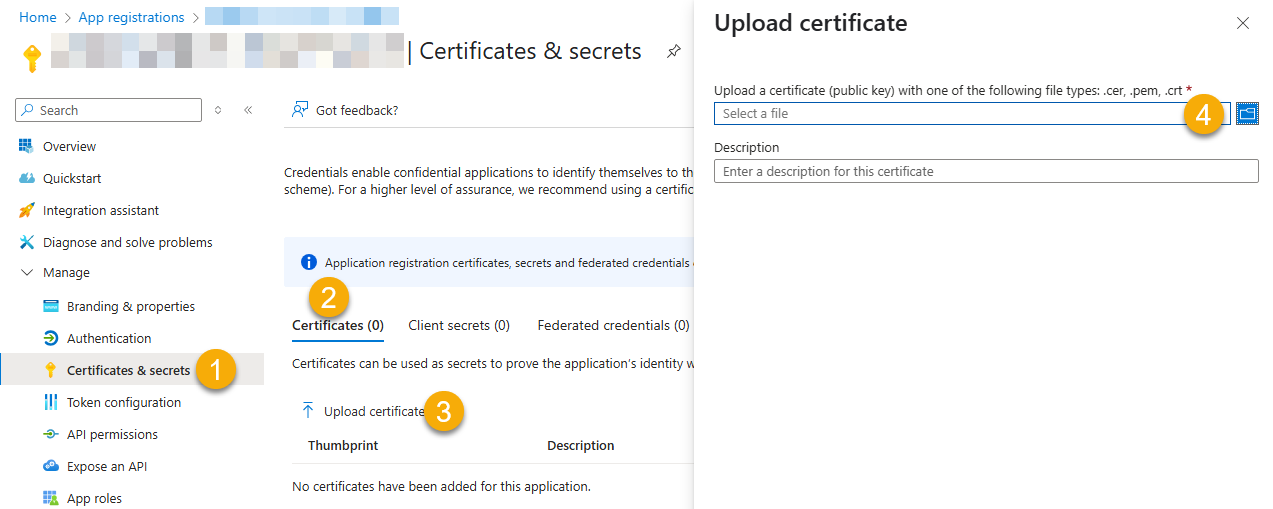
- Click Select a file (Browse button)
- Select public key file (*.cer) from local machine and click OK to upload
Configure ZappySys Connection - Use private key (i.e. *.pfx or *.pem)
Now its time to use certificate pfx file (private key) generated in the previous step (NOTE: PFX file contains both private key and public key).-
Go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- Configure private key
- go to Certificate Tab
- Change Storage Mode to
Disk File: *.pfx format (PKCS#12).NOTE: You can also useStored In LocalMachinemode if PFX file already imported in the Local Certificate Storage Area - User Store OR Machine Store. If you used OpenSSL to generate key pair then useDisk File: *.pem format (PKCS#8 or PKCS#1)Mode for Cert Store Location. - Supply the key file path
- Supply the certificate password (same password used in earlier PowerShell script)
- Now go back to General Tab, choose Default Group / User Id and Default Drive Id from the drop down menu.
- Click Test connection see everything is good
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Application Credentials with Certificate (Sign JWT with Private Key) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
OneDriveApplication Credentials with Certificate (Sign JWT with Private Key) [OAuth]https://graph.microsoft.com/v1.0Required Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Certificate: *** Configure [Client Certificate] Tab *** Fill-in the parameter... Default Group or User Id (additional Scopes needed to list - If fails enter manually) Fill-in the parameter... Default Drive Id Fill-in the parameter... Optional Parameters RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429|503|423 RetryCountMax 5 RetryMultiplyWaitTime True Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) Extra Headers (e.g. Header1:AAA||Header2:BBB) IsAppCred 1  Find full details in the OneDrive Connector authentication reference.
Find full details in the OneDrive Connector authentication reference. -
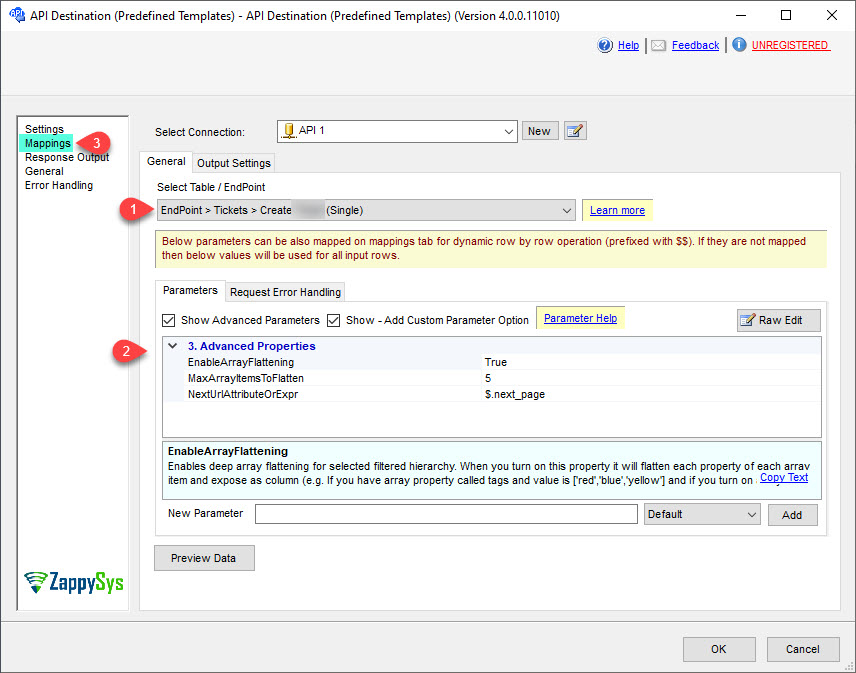
Select the desired endpoint, change/pass the properties values, and go to the Mappings tab to map the columns.
API Destination - OneDriveRead and write Microsoft OneDrive data effortlessly. Integrate, manage, and automate files and folders — almost no coding required.
-
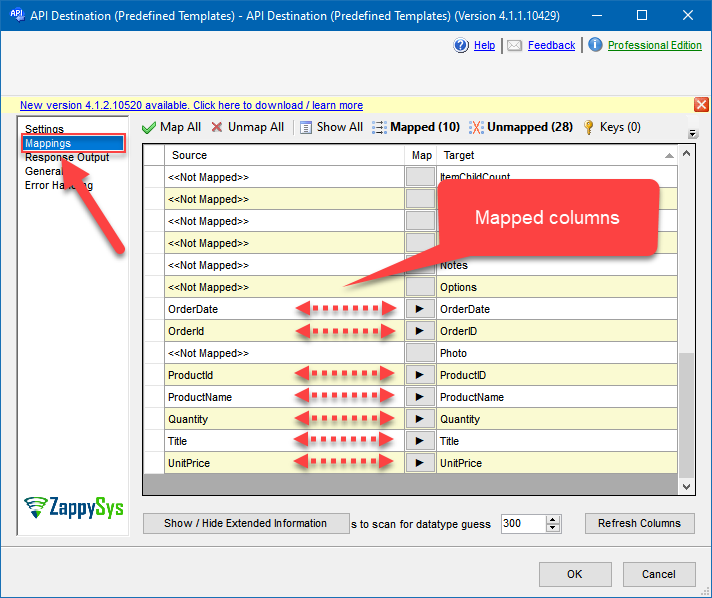
Finally, map the desired columns:
API Destination - OneDriveRead and write Microsoft OneDrive data effortlessly. Integrate, manage, and automate files and folders — almost no coding required.
-
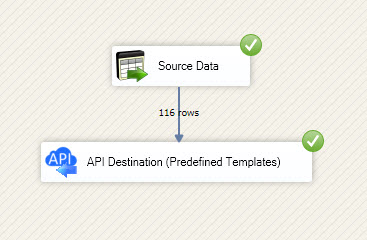
That's it; we successfully configured the POST API Call. In a few clicks we configured the OneDrive API call using ZappySys OneDrive Connector
Load OneDrive data into SQL Server using Upsert Destination (Insert or Update)
Once you configured the data source, you can load OneDrive data into SQL Server using Upsert Destination.
Upsert Destination can merge or synchronize source data with the target table.
It supports Microsoft SQL Server, PostgreSQL, and Redshift databases as targets.
Upsert Destination also supports very fast bulk upsert operation along with bulk delete.
Upsert operation
- a database operation which performs INSERT or UPDATE SQL commands
based on record's existence condition in the target table.
It
Upsert Destination supports INSERT, UPDATE, and DELETE operations,
so it is similar to SQL Server's MERGE command, except it can be used directly in SSIS package.
-
From the SSIS Toolbox drag-and-drop Upsert Destination component onto the Data Flow designer background.
-
Connect your SSIS source component to Upsert Destination.
-
Double-click on Upsert Destination component to open configuration window.
-
Start by selecting the Action from the list.
-
Next, select the desired target connection or create one by clicking <New [provider] Connection> menu item from the Target Connection dropdown.
-
Then select a table from the Target Table list or click New button to create a new table based on the source columns.
-
Continue by checking Insert and Update options according to your scenario (e.g. if Update option is unchecked, no updates will be made).
-
Finally, click Map All button to map all columns and then select the Key columns to match the columns on:
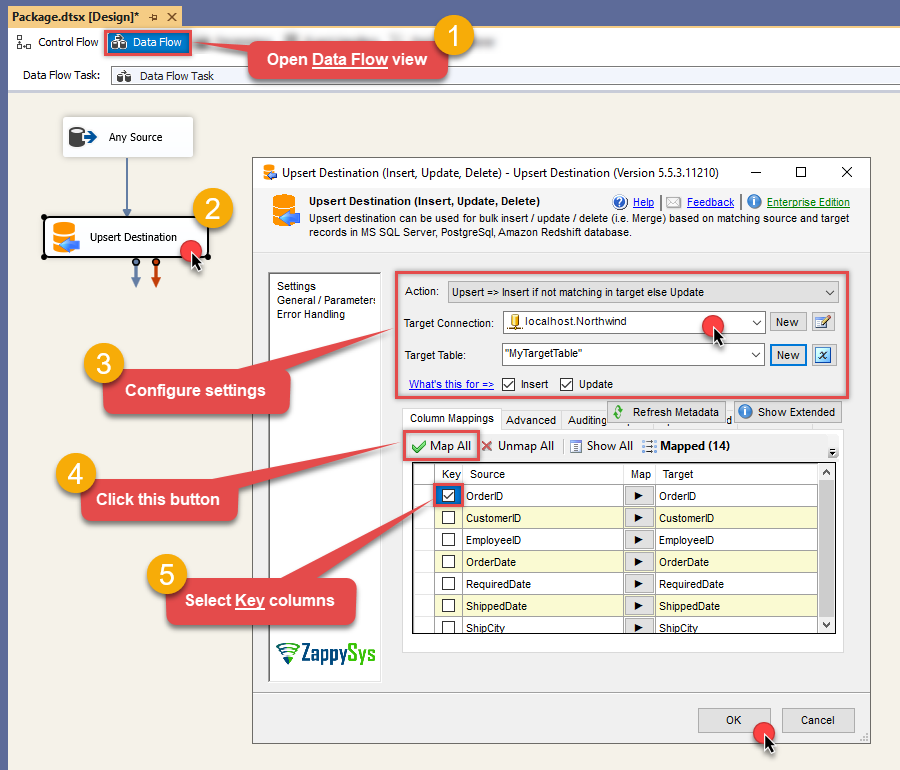
-
Click OK to save the configuration.
-
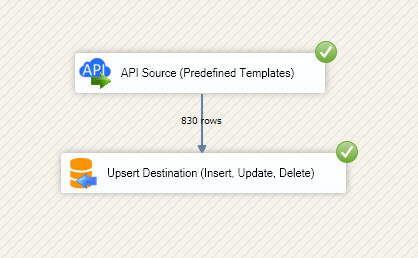
Run the package and OneDrive data will be merged with the target table in SQL Server, PostgreSQL, or Redshift:
-
Done!
Deploy and schedule SSIS package
After you are done creating SSIS package, most likely, you want to deploy it to SQL Server Catalog and run it periodically. Just follow the instructions in this article:
Running SSIS package in Azure Data Factory (ADF)
To use SSIS PowerPack in ADF, you must first prepare Azure-SSIS Integration Runtime. Follow this link for detailed instructions:
Explore supported OneDrive Connector actions
Got a specific use case in mind? We've mapped out exactly how to perform a variety of essential OneDrive operations directly in SSIS, so you don't have to figure out the setup from scratch. Check out the step-by-step guides below:
- Copy item (File or Folder)
- Create / Update CSV File (Generic)
- Create / Update JSON File (Generic)
- Delete Item (File or Folder)
- Download File
- Get Groups
- Get Item (File or Folder)
- Get User Drives
- Get Users
- List Drives
- List Excel Files
- List Excel Worksheets of a File (i.e. List Tabs)
- List Files
- List Root (Non Recursive)
- Lists Folder Items (Non-Recursive Children)
- Move or rename item (File or Folder)
- Read CSV File (Generic)
- Read Drive
- Read Excel Worksheet (Auto Detect Range)
- Read Excel Worksheet (From Exact Range)
- Read JSON File (Generic)
- Upload File
- Make Generic REST API Request
- Make Generic REST API Request (Bulk Write)
Conclusion
In this article we showed you how to connect to OneDrive in SSIS and integrate data without writing complex code — all of this was powered by OneDrive Connector.
Download SSIS PowerPack now or ping us via chat if you have any questions or are looking for a specific feature (you can also reach out to us by submitting a ticket):